Sophos Firewall OS (SFOS) Update v17.5 - MR4 veröffentlicht
Sophos hat die Version 17.5 MR4 für das Sophos Firewall OS (SFOS) veröffentlicht.
Hinweis: Für weitere Informationen zum Upgrade schaut euch folgenden Post an: SFOS Firmware auf Sophos Firewall aktualisieren.
Backup-Verschlüsselung
Mit MR4 kommt eine Funktion auf die XG, welche UTM-User bereits seit Jahren kennen. Die Backups können nun verschlüsselt werden. Mit etwas Mühe konnte man bisher das Admin-Passwort aus einem SFOS-Backup auslesen. Sophos sagt hier, dass die Konfiguration bis anhin mit einem allgemeinen Passwort verschlüsselt wurde, welches nur Sophos kannte. Daher haben wir in der Vergangenheit auch eher davon abgeraten, sich die Backups via E-Mail zuzusenden oder auf einen FTP-Server zu laden.
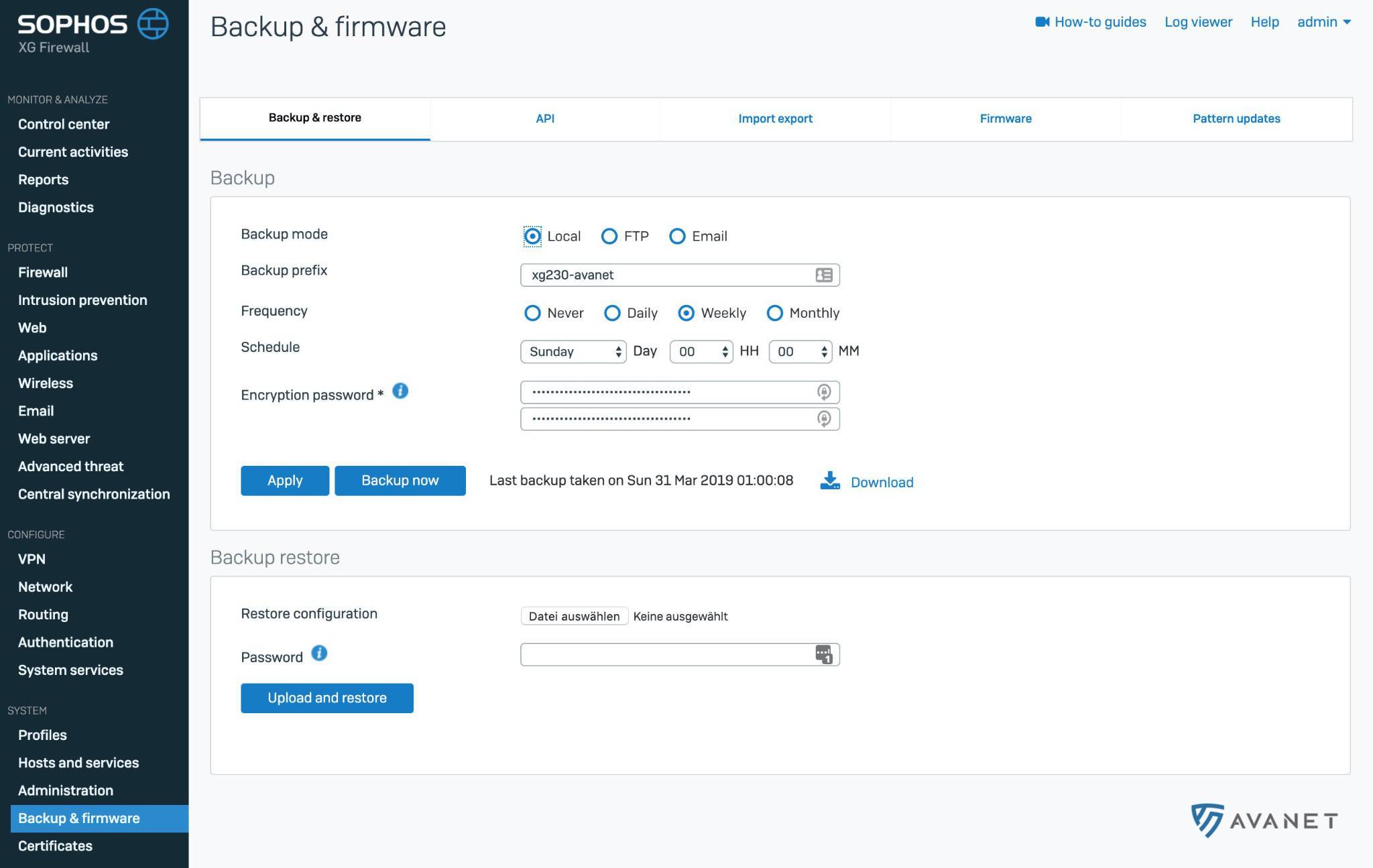
Wir empfehlen, das Admin-Passwort zu ändern und ein sicheres Passwort zu erstellen, damit die Konfigurations-Backups zukünftig verschlüsselt werden. Danach kann man sich die Backups dann auch mit gutem Gewissen per E-Mail zusenden oder auf einen FTP-Server laden.
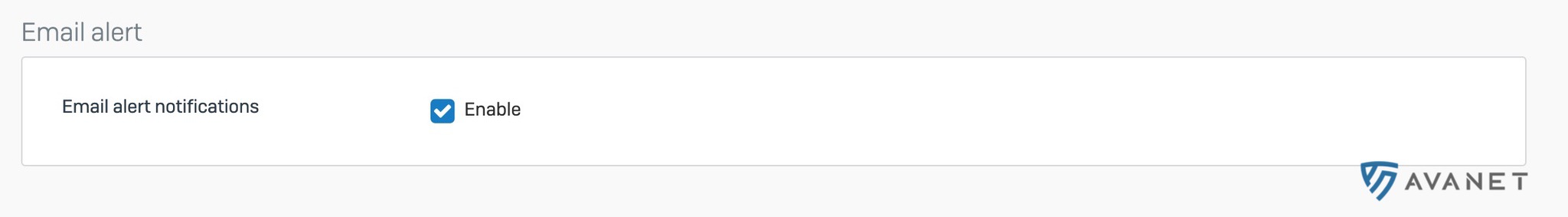
Benachrichtigungen
Die E-Mail-Benachrichtigungen auf der XG sind aktuell praktisch nicht vorhanden. Sophos arbeitet jedoch daran, dass diese zukünftig noch verbessert werden. Mit der neuen XG-Firewall-Firmware gibt es nun erste Verbesserungen.
Weitere kleine Verbesserungen
- Es gibt nun die Möglichkeit, die Anwendungskonfigurationsdatei aus der XG Firewall-Konsole heraus zu generieren und in GSuite zu importieren. Ihr findet sie unter Authentifizierung > Dienste > “GSuite App Config herunterladen”.
- GRE- und RED-Schnittstellenunterstützung für PIM-SM hinzugefügt.
- Unterstützung für “DHE key exchange cipher suites” mit HTTPS-Scanning.
Fehlerbehebungen
- NC-28883 [Authentication] Able to change group membership of backend users when authserver doesn’t exist anymore
- NC-38834 [Authentication] access_server service getting restarted due to heartbeat found dead
- NC-39735 [Authentication] User under an OU falls under OPEN GROUP upon authentication
- NC-40072 [Authentication] Not able to delete surfing quota profile, delete opcode search for accesspolicyid instead of surfingquotapolicyid
- NC-40945 [Authentication] Failed and successful Logins at the same time
- NC-42329 [Authentication] Unable to upgrade from v17.1 MR4 to v17.5 GA
- NC-34479 [CSC] Virtual XG randomly rebooting - snort using up all swap
- NC-39990 [DHCP] When statically assigning an IP to a devices on multiple DHCP scopes, the gateway settings are pulled from the first one
- NC-34039 [Email] Websites are blocked by Sophos AV because of reason “Malware”
- NC-38555 [Email] File Protection can’t block MIME type doc
- NC-38840 [Email] Unable to delete a particular email which was quarantined
- NC-40071 [Email] GUI option for offline relate on/off for inbound mails
- NC-40131 [Email] Mail downloaded from error queue doesn’t get displayed properly in mail client
- NC-40364 [Email] Personal email exception manipulation by other authenticated users
- NC-40389 [Email] Mails released from spool get an incorrect firewall rule ID
- NC-40666 [Email] Coredump in mailscanner
- NC-41061 [Email] SPX encryption leads to “carriage return and line feed” in attachments
- NC-41574 [Email] SPF should get applied on inbound mail sent from protected domain to protected domain from internet
- NC-41862 [Email] Mail log on GUI does not show delivered mails
- NC-42409 [Email] Bounce back mail due to recipients having MX records which point directly to an IP
- NC-43353 [Email] smtpd behavior is different from 17.1 to 17.5 (without subscription)
- NC-43703 [Email] Warren service unable to load EC type CA certificate.
- NC-35350 [Firewall] PPPoE interface status remains in status “Connecting” for 2 hours
- NC-39522 [Firewall] Network protection options in setup wizard of XG are misleading
- NC-39605 [Firewall] Modifying one time schedules fails, if timer has already triggered
- NC-39907 [Firewall] API command to enable SpoofProtection is not working
- NC-40176 [Firewall] Firewall rule is listed in business application rule destination network objects
- NC-40622 [Firewall] Incomplete MAC address shown in Log Viewer
- NC-41316 [Firewall] Update country host DB
- NC-41389 [Firewall] HA - system doesn’t send out garp upon failover
- NC-41632 [Firewall] Business Rule - port translation not working as expected
- NC-41652 [Firewall] Unable to delete vlan interface - “Interface could not be deleted”
- NC-42342 [Firewall] One time timer are executed before expected time
- NC-39813 [FQDN] Unable to use underscore in FQDN host creation
- NC-37771 [Hotspot] Duplicate vouchers in export files
- NC-38004 [Hotspot] Hotspot password of the day is not getting reflected into run time config
- NC-38120 [IPsec] L2TP over IPsec is sending keepalives forever
- NC-38746 [IPsec] S2S connection is not initiated after DHCPv6 interface update
- NC-39267 [IPsec] IE11: cannot create and update IPsec policy
- NC-41299 [IPsec] IPsec SA is updated with incorrect SA information
- NC-42099 [IPsec] Sophos Connect Client cannot connect to Sophos Connect Client policy using digital certificates
- NC-42290 [Licensing] Additional CPU cores not detected in v17.5 after license upgrade (NC-26328)
- NC-40282 [Logging Framework] High CPU usage from garner / active.db grows continuously
- NC-34323 [RED] HA active-active routing issue over RED S2S tunnel
- NC-42159 [RED] Validation of provisioning file failed
- NC-40444 [RED_Firmware] Tunnel compression does not work
- NC-38899 [Reporting] Scheduled custom mail reports received via email does not show the mail size
- NC-40303 [Reporting] Log Viewer is not loading new logs after screen unlock
- NC-40983 [Reporting] Follow-up for NC-26459: Reports for “Traffic Insight” not shown on dashboard
- NC-41788 [Reporting] Unable to upload custom logo
- NC-41232 [SecurityHeartbeat] Heartbeat status on XG showing “at risk” instead of “green”
- NC-36776 [Synchronized App Control] New Apps number doesn’t match the displayed list entries
- NC-37423 [Synchronized App Control] SAC Tab fails to load for high number of EPs and APPs
- NC-37815 [UI Framework] Guest User expiration is not correctly ordered
- NC-40158 [WAF] Disable TLS session tickets
- NC-34088 [Web] Application control shows blocked applications when they are not blocked
- NC-38892 [Web] Inappropriate description in web category for “Society & Culture”
- NC-39517 [Web] Webfilter memory usage is growing over time and not going down
- NC-39817 [Web] Application filtering using “Smart Filter” filter disappear randomly
- NC-40265 [Web] Unable to run web policy test for generic top level domains
- NC-40503 [Web] Web filter policies not getting updated after CR to SFOS migration
- NC-42264 [Web] Garner on Aux node dead after upgrade to v17.5
- NC-43056 [Web] Policy tester activities shows junk characters in result with file download is blocked
- NC-38368 [Wireless] APs randomly going to INACTIVE STATE
- NC-38868 [Wireless] Time based scan with DCS is not showing after configuration for 5.0Ghz
- NC-39840 [Wireless] Wireless interface going to UNPLUGGED STATE
- NC-39986 [Wireless] 5 Ghz band is not available in AP setting while country set to Qatar
- NC-40091 [Wireless] Disable TCP Segmentation Offload for separate zone interface
- NC-38085 [WWAN] Unable to detect 4G USB Modem D-Link DWM-222 A1 on XG 125 and XG 85 with HW Rev.3

