Sophos Zero Trust Network Access – an alternative to VPN
Sophos has recently released the public beta of its new product, Sophos Zero Trust Network Access (ZTNA). Anyone can now sign up for the ZTNA Early Access Program. Let’s look at what the zero‑trust security model is and what makes it one of the most secure cybersecurity frameworks in the world.
What is the zero-trust model?
Put simply, the zero‑trust model states that a company cannot trust every request to access data and must always verify the source first. To sum it up in three words: trust no one. Do not grant anyone access to your network unless you know 100% who wants to access your data and you actively agree to it.
Why would you want to use this seemingly excessive and almost paranoid security model? Consider that Cybersecurity Ventures predicted cybercrime would cause 6 trillion US dollars in damage worldwide by 2021. That is the expected loss despite the heavy investments in cybersecurity made by some of the world’s largest companies. No one is completely safe from cyberattacks, SQL injections and unauthorized access.
The zero‑trust model proposes a change to the traditional concept where organizations focus on threats from the outside while assuming that anything already inside the network needs no further authorization and is harmless. Most security breaches happen because, once access has been granted, it is easy for attackers to move laterally and reach additional information inside the system. Before you put your full trust in the zero‑trust model, it is worth weighing up the pros and cons of this framework.
Advantages of the zero-trust model
- The organization is far less vulnerable to cyberthreats.
- Authentication processes are very strict.
- Improved protection for corporate data.
- Highly sophisticated security structure.
Disadvantages of the zero-trust model
- Requires a lot of time to set up.
- Managing many users is demanding because every access request has to be authenticated.
- Data backups become more complex because data is stored in multiple locations.
What is ZTNA?
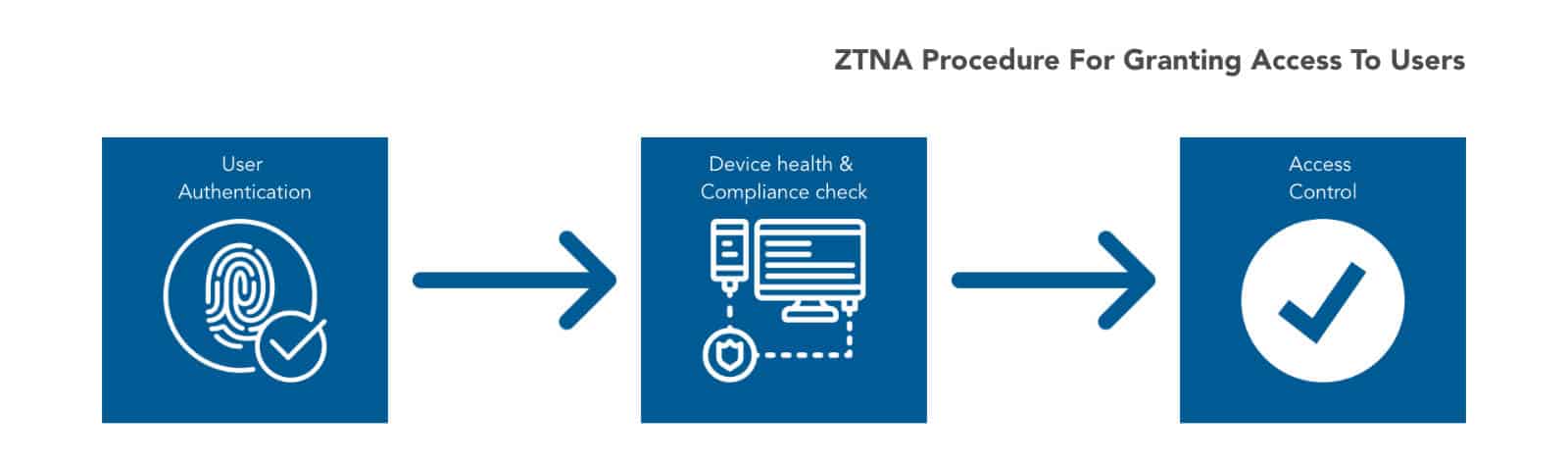
ZTNA is the latest Sophos Central product, delivered and managed entirely in the cloud. Its purpose is to provide remote users with secure access to applications. What does ZTNA actually do? It is based on the zero‑trust framework, which means that the user is verified in every reasonable way to minimise the risk of compromise. This includes user authentication (typically two‑factor authentication to ensure that stolen credentials cannot easily be misused), validation of the device posture and checking the device’s compliance status to decide whether to grant access.
How does ZTNA compare with VPN?
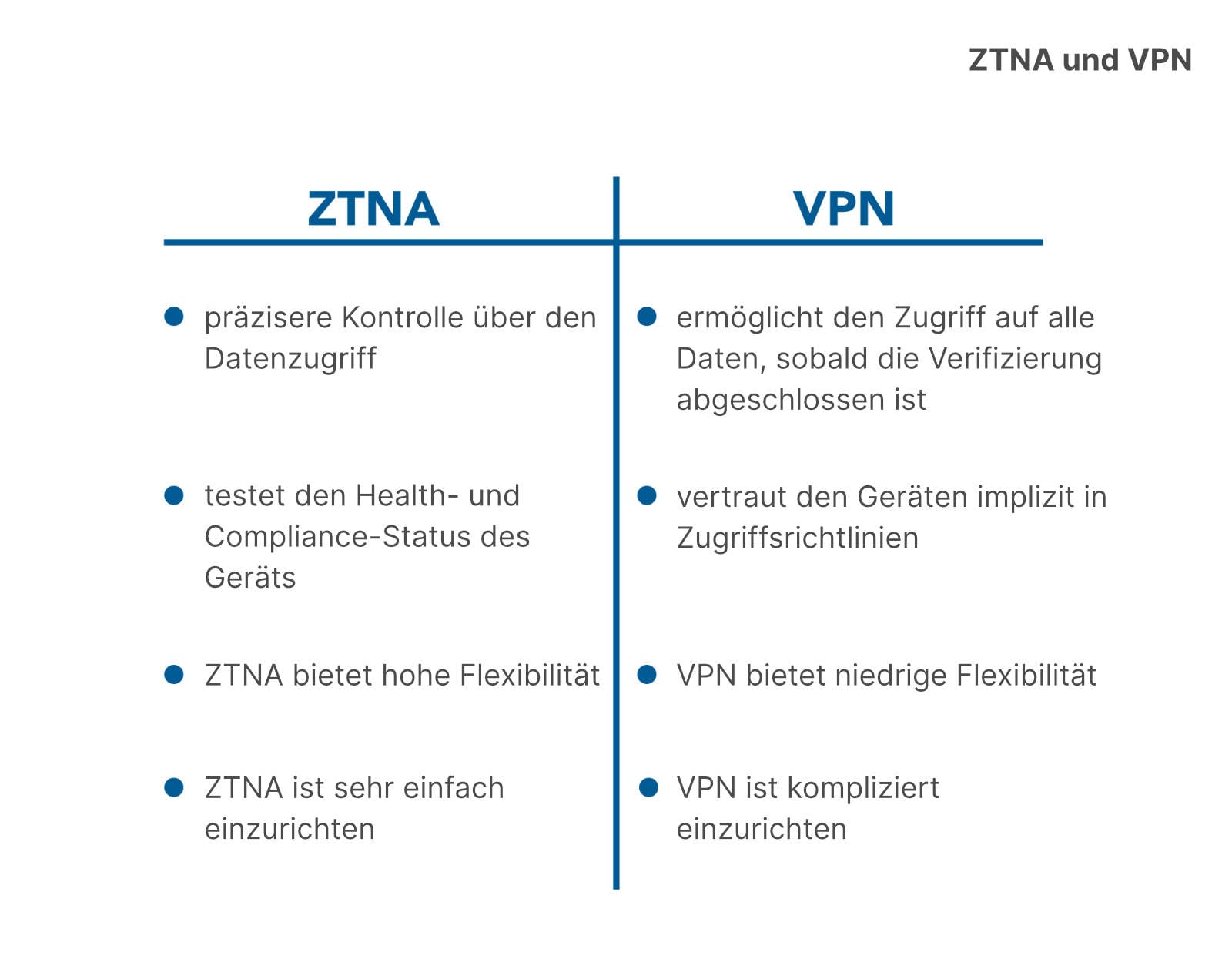
While VPN has served us well, ZTNA offers a better solution when you compare them side by side. Where does ZTNA outperform VPN?
- Better security: Security for connected applications improves significantly because, unlike VPN, ZTNA also verifies device integrity and device status. Compromised devices can cause serious damage to other systems.
- Transparent: ZTNA provides users with a transparent experience and smooth connection management. VPN can be cumbersome to use and tends to generate support calls.
- Granular control: ZTNA offers segmented access to application data, whereas VPN generally grants access to the entire network once authentication has completed. Attackers like this: once they are in, they have plenty of time to move from device to device. After a single successful authentication, they may be able to reach thousands of devices.
Because VPN is a technology that was developed more than 20 years ago, it is starting to feel outdated. It was originally designed to extend trusted networks and connect company employees in a unified network. Today, however, cloud‑based applications are accessed by large numbers of users from multiple devices, which makes VPN a vulnerable and unsafe choice. Attackers repeatedly exploit these weaknesses, and VPN vulnerabilities have become a serious risk for organizations.
Which applications can ZTNA protect?
ZTNA protects connected applications that are hosted in a company’s own networks or made available in the public cloud. This includes applications such as wikis, Jira or any other type of repository or ticketing app. ZTNA does not protect applications that are not owned by the customer.
Components of ZTNA
Sophos ZTNA consists of three main components:
- Sophos Central: provides a cloud management platform for all Sophos products, including Sophos ZTNA. It is cloud‑ready and makes deployment, policy management and reporting straightforward.
- Sophos ZTNA Gateway: a virtual appliance that protects on‑premise or public‑cloud‑connected applications, with initial support for AWS and VMware ESXi and support for Azure, Hyper‑V and Nutanix coming soon.
- Sophos ZTNA Client: provides seamless connectivity to applications based on end‑user identity and device posture. It is easy to roll out and reads device posture information from Windows Security Center. Initially it will only support Windows; support for macOS, Linux and the mobile operating systems iOS and Android will follow.
When will Sophos ZTNA be available?
Sophos has already launched the Early Access Program for Sophos Zero Trust Network Access (ZTNA). The first phase enables clientless access to browser‑based applications such as CRM and ticketing systems (for example JIRA). The next phase will add further enhancements such as a Windows client with integrated deployment alongside Intercept X, Synchronized Security for device health, additional identity providers and an AWS gateway.
Licensing and pricing
As with other Sophos Central products, ZTNA is licensed per user rather than per device. A user with multiple devices therefore only needs a single license. At launch, there will also be a free trial so that organizations can look under the hood before deciding whether to purchase licenses.

