Sophos Central Endpoint Intercept X - The Solution Against Ransomware
Let’s face it: the moment you connect a computer to the internet today, it is exposed to a vast range of threats. Effective protection for you and your network requires a combination of common sense, a robust antivirus solution and, ideally, a firewall with a web filter at the network perimeter. Shutting down your computer at night without having picked up some form of malware is becoming increasingly difficult.
Since November 2015, ransomware has been making headlines, and for a long time there was no technical protection available - only tips and advice for IT managers. With Sophos Intercept X, Sophos has now launched a product that complements your existing endpoint security solution and can protect against ransomware, zero‑day exploits and stealth attacks.
In this blog post we’ll leave the classic viruses, worms and Trojans to one side and focus on the really nasty category - so‑called ransomware (crypto‑Trojans). We’ll also show how Sophos can protect against this type of malware and which products you need for that.
So what exactly is ransomware?
Imagine you innocently open an email attachment and a message suddenly appears on your screen saying your data has just been encrypted and you will only get it back if you pay a “ransom”. But you are not asked to pay using familiar methods such as PayPal, credit card or bank transfer; the transaction must be as anonymous and untraceable as possible. As if the situation were not stressful enough already, you now also have to deal with Bitcoins. Pretty brazen, isn’t it?
Ransomware - when you suddenly have to pay a ransom for your own data.
Today’s attackers have found an incredibly effective way to make a lot of money in a very short time. The attacker - or more accurately, the attacker organisation - gains enough financial resources to reinvest part of that income in spreading ransomware even further. The risk that you, or even your company, will become a victim is steadily increasing. Consider for a moment what your company data would be worth to you.
In the following video, Sophos explains the topic in 90 seconds:
Ransomware is not going away
Ransomware is currently the most effective type of attack, which means it will not disappear any time soon. Your data is encrypted and, if you want it back, you have to pay. Private users have valuable data too, not just companies, so everyone is at risk. Companies are simply more exposed because many users access the same data. It only takes one employee to be infected for the shared drive to be encrypted and the company’s operations to grind to a halt. For attackers, ransomware is a success story - it is a multi‑billion‑dollar business. If you have not taken action yet, you really should.
How can you protect yourself against ransomware?
When “ransomware” first became a public issue, numerous guides for IT managers explained what could be done about these crypto‑Trojans. In essence, the advice was to train staff, actively raise awareness of the threat and perform regular backups of company data. There was no software solution that could reliably detect such Trojans. Antivirus vendors were overwhelmed by these new, highly sophisticated Trojans - and some still are today. Sophos was the first, in December 2015, to release Sophos Sandstorm as a solution for defending against Advanced Persistent Threats (APTs) and zero‑day malware. That was at least a start. If you want to protect yourself against ransomware, we recommend the brand‑new product Sophos Intercept X which, in our view, should be installed on every endpoint.
Update: In the meantime, the new products Intercept X Advanced and Intercept X Advanced for Server are available.
Using Sophos Intercept X against ransomware
From our perspective, Sophos Intercept X is simply essential if you want effective protection against these new threats. Intercept X is based on technology from the security vendor SurfRight, which was acquired last year. The first product resulting from this acquisition was Sophos Clean. With Intercept X, this technology has now also been integrated into Sophos Central and enhanced with new capabilities. For detecting threat patterns, it relies on behaviour analysis, attack vectors and big data. This allows malware to be identified without depending on updates or signatures. Signatureless detection also has the advantage of protecting against unknown malware and attacks using zero‑day exploits.
CryptoGuard - an anti‑ransomware innovation
One component of Intercept X is CryptoGuard. This feature protects against ransomware and instantly detects when files are being encrypted. When this happens, file encryption is blocked and any files that have already been encrypted are automatically restored so that no data is lost.
The killer feature is the analysis
The real highlight comes at the end. Imagine that, despite all your protection measures, some malware still makes its way into your network. How did this happen? Which devices were infected, and what should you do now? The “Root Cause Analysis Tool” from Intercept X can answer all of these questions in great detail. A visual, 360‑degree analysis helps you identify where the attack took place, which system components were affected and at which point it could have been stopped. It also provides recommended actions for dealing with similar attacks in future.
Additional protection alongside your existing antivirus
Choosing the right antivirus package can be almost overwhelming. There is Symantec, McAfee, Kaspersky, Trend Micro, Avira, Avast and many more. The chances are high that you are already using one of these products. With Intercept X you do not have to change that. In fact, that is exactly the idea: Sophos Intercept X can - and really should - be installed alongside existing endpoint security solutions from any vendor, thereby raising your overall security level.
Intercept is not an alternative to an antivirus; it is an additional protection layer.
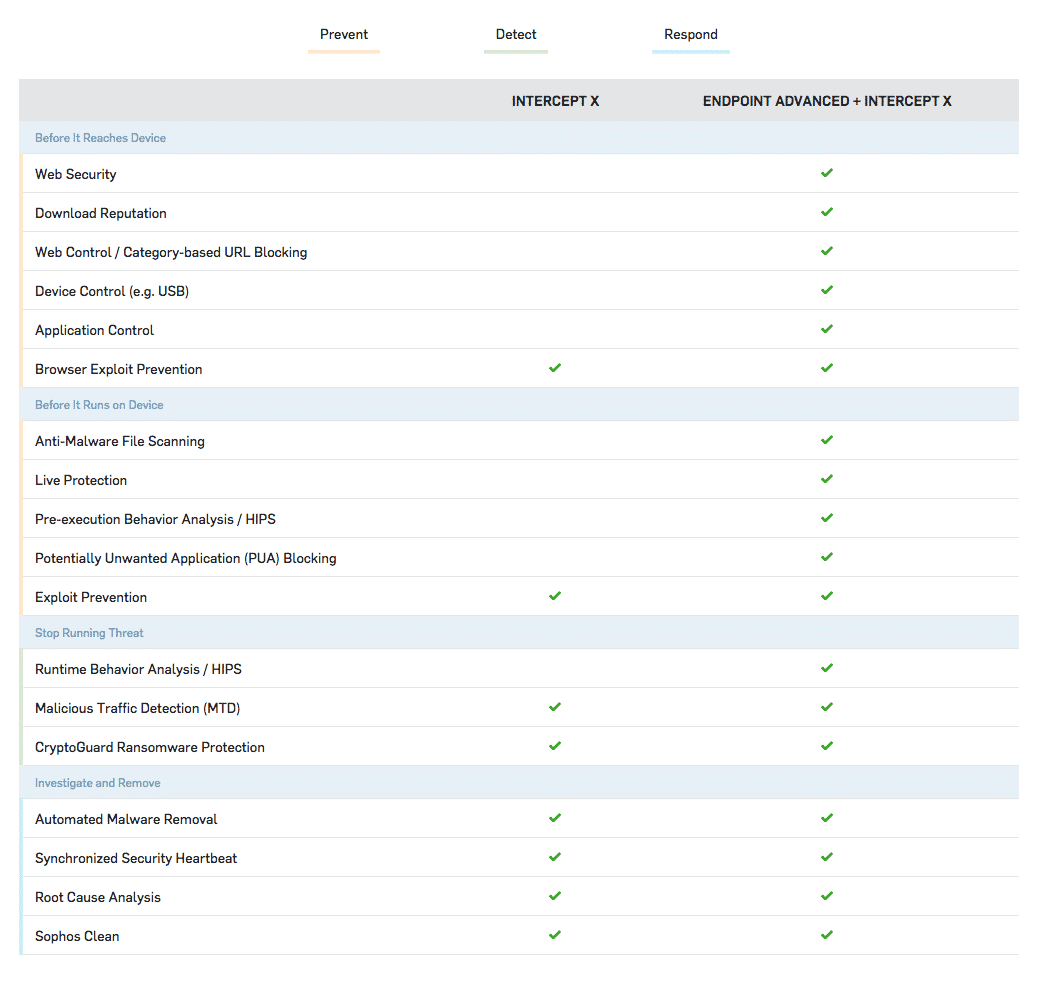
Sophos Intercept X can of course also be used together with Sophos Central Endpoint Standard (new!) or Advanced, providing a powerful additional layer of protection.
Managing Intercept X
Intercept X can be deployed and managed via the cloud‑based management console Sophos Central. Administrators can control and configure settings, assign licences, add new endpoints and monitor all activity.
System requirements
Intercept X works seamlessly alongside your existing antivirus software, whether that is McAfee, Kaspersky, Symantec, Trend Micro, Avira, Avast or another endpoint protection solution.
According to our contact at Sophos, a Mac solution is on the way and will also be integrated into Intercept X.
Try Sophos Intercept X now!
To get your own impression of Sophos Intercept X, you can test it free of charge for 30 days. All you need is a Sophos Central account.
If you do not yet have a Sophos Central account, you can create one on the Sophos website and test all functions, including “Sophos Intercept X”, free of charge for 30 days.
If you already have a Sophos Central account and your 30‑day trial has expired, you can either order a licence for “Sophos Intercept X” from our shop, or choose our “Sophos Central subscription” and rent the licences on a monthly “pay‑as‑you‑go” basis:
Ransomware simulator
If you are still not entirely convinced and feel that you are protected against ransomware even without Intercept X, take a look at the independent, free test tool “RanSim” from KnowBe4. With this tool you can test whether your system could be compromised by ransomware.