Sophos SFOS SQL injection vulnerability fixed
A security vulnerability was discovered in Sophos Firewall OS that attackers were already exploiting. Sophos has pushed out a hotfix, but firewall administrators still need to change all local passwords.
What happened?
At first glance, it may seem contradictory that a firewall intended to protect an IT infrastructure can itself be vulnerable. In practice, however, the rule is simple: any system that runs software can contain vulnerabilities – they just may not have been discovered yet.
On 22 April 2020 at 20:29, a user reported a zero‑day vulnerability to Sophos. At that point, the attack had already been running for around five hours. It was noticed because suspicious activity became visible in the admin portal. The report to Sophos quickly had an effect: by around 22:00, the first domains were blocked. In parallel, the root cause was identified and work on a hotfix began. On 25 April 2020 at 07:00 – roughly 63 hours after the first attacks – a hotfix was rolled out to all firewalls running SFOS.
Attackers on the internet could use the vulnerability to obtain local usernames, including password hashes. In the worst case, this could have allowed them to gain access to the firewall, provided they had first successfully cracked the password hash. The incident is another reminder of how important it is to use long, complex and secure passwords.
Who was affected?
All systems running Sophos Firewall OS (SFOS) were potentially affected – including SG appliances, XG firewalls and virtual installations. These systems were at risk, although that does not automatically mean they were compromised.
Particularly critical were firewalls whose HTTPS admin service or user portal was reachable from the internet (see screenshot below). If the default setting was changed so that another firewall service – for example SSL VPN – listens on the same port as one of the portals, this configuration was also affected.
What needs to be done?
The Trojan, called Asnarök, exploited a previously unknown (zero‑day) pre‑auth SQL injection vulnerability. Sophos strongly recommends changing all local passwords on the firewall. This means the admin password and all other passwords for users that were created directly on the firewall. Accounts that are synchronised to the firewall from an Active Directory, for example, are not affected.
- Change the admin password (super admin password of the firewall)
- Reboot the firewall
- Change all other local passwords
For customers with a maintenance contract, all the necessary steps have already been carried out.
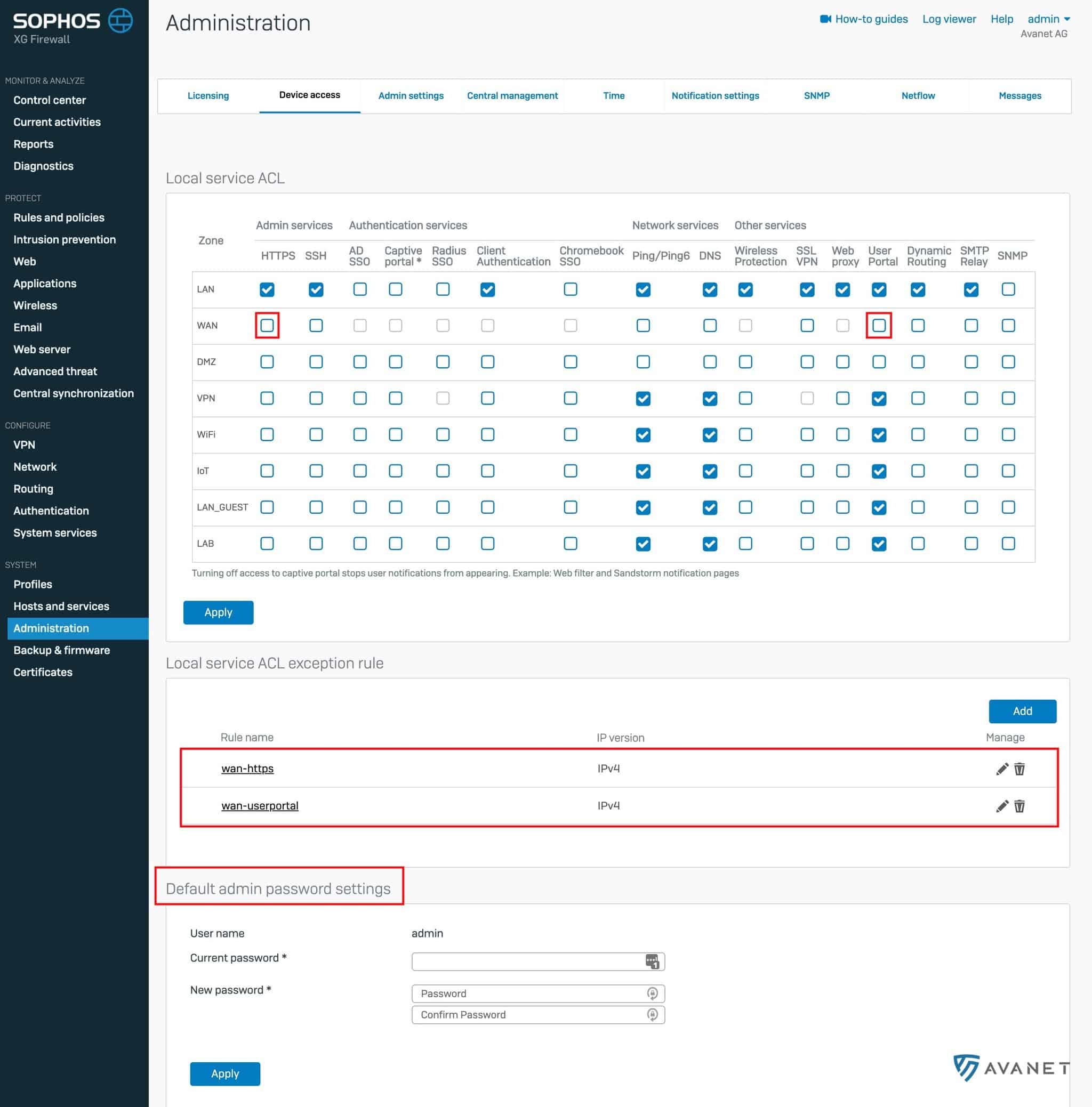
- The screenshot shows which checkboxes should not be enabled – these would allow access to the firewall from the internet.
- Further down, you can define manual rules so that access to the firewall is only allowed from a specific IP address, for example. That significantly increases security.
- At the bottom, you can see where the admin password can be changed.
Hotfix
Sophos has distributed the hotfix that closes the vulnerability via automatic updates. Automatic installation of updates is enabled by default.
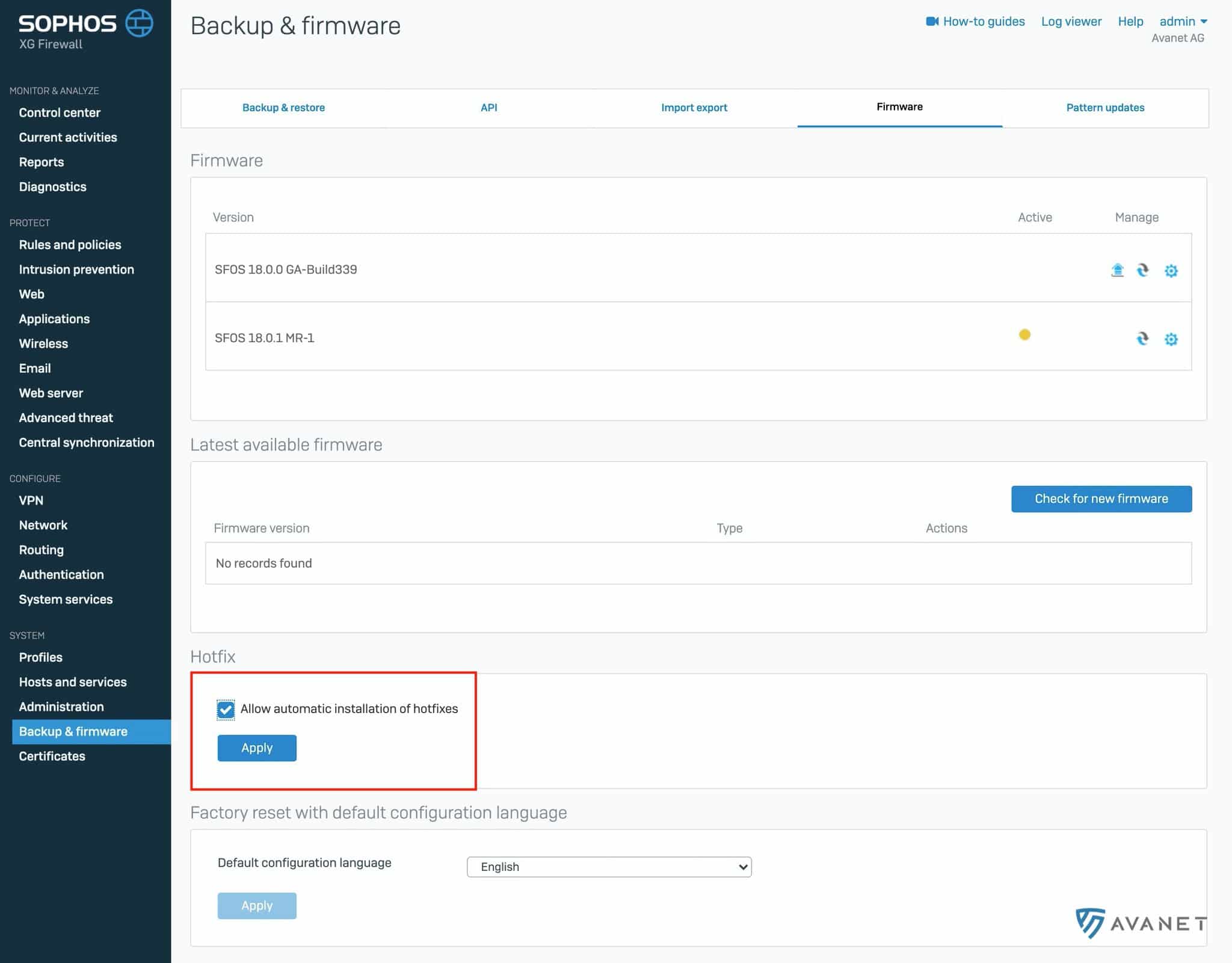
All firewalls running SFOS 17.x or later received the patch. If your firewall is still running version 15 or 16, it is affected as well and should be updated without delay.
More information
If you read our blog regularly, you already know that we spend our days working with Sophos products and earn our living through services and support around them. Even though there is a saying that you should never bite the hand that feeds you, we make a point of not looking at everything through rose-tinted glasses. We write what we think, and that can absolutely include critical remarks. So, without sugar-coating anything, here is our honest assessment as always:
In our view, Sophos communicated very quickly and very transparently here. Many other vendors remain extremely vague and you never really find out what happened.
Sophos informed the community within a short time through both a knowledge base article and a blog post. As a Sophos partner, we also received an email on Sunday, in fact eight copies of it. The information therefore came directly from the vendor first and was not spread exclusively through news sites, which is far from standard in the security world.
The knowledge base contains all the details of the incident and the recommended steps. This blog post focuses on the key points, which are sufficient for many environments.