7 Reasons Why the XG Firewall (SFOS) Is Better Than the UTM
For over two years, we have only deployed XG Firewalls with SFOS or installed SFOS on SG Appliances. Admittedly, the XG Firewall was an absolute horror show in the first versions and could only be used effectively in a few environments. With version 16, things slowly improved and we dared to implement smaller projects with it. From v16.5 onward, we then fully relied on the XG for new projects and have never looked back at the UTM since.
To clear things up right at the beginning: When I speak of the XG Firewall, I mean the XG Appliance series with the Sophos Firewall OS (SFOS). However, we also support SG Appliances on which we have simply installed SFOS. This works perfectly. 🙂
After having already implemented several projects with the XG Firewall, I wanted to share 7 reasons why, in my opinion, the XG Firewall is a better choice than the SG series with the UTM operating system. With this article, I would like to contribute my share to the UTM vs. XG debate. 🥊
01 - Development
When I look for a new app for my smartphone or computer today, I pay particular attention to when the app was last updated. If I don’t find a changelog, I look at the social account, e.g., Twitter. Any activity older than a year is dead to me, and the app definitely won’t make it onto my smartphone or computer.
Admittedly, with the UTM Firewall, it is not quite that bad. But the update cycles have become extremely stretched out. Previously, there was an update for the UTM almost every month. Today, it is roughly every 4 months, and new features are practically non-existent.
The reason for this is as follows: Sophos has about 300 developers working on the SFOS and UTM operating systems. However, only about 5% of these developers still work on the UTM operating system. The rest work on the XG Firewall. This also shows where the manufacturer’s priorities lie.
From time to time, UTM users are given a little hope with a new feature. But in reality, Sophos has long been looking for a way to make the XG appealing to loyal followers without losing them to another manufacturer. As a former UTM user, however, I know that you do not switch systems quickly unless you really have to. So, as long as the UTM is not officially discontinued, there is simply no reason for the majority to switch.
If you look at the roadmap of the two operating systems, the list for SFOS is extremely long and the plans extend far beyond 18 months. With UTM, features have been removed from the roadmap in the past or constantly pushed back. A prominent example here is IKEv2. The feature was on the roadmap for a long time, was constantly postponed, and ultimately even completely removed from the roadmap. After an outcry in the community, it was re-added and is now scheduled to appear in version 9.8 next year.
With Sophos Firewall OS, things look completely different, and that is the first reason why we love the system. Approximately every seven weeks, we can look forward to new MR - Maintenance Releases, and once or twice a year there is a MINOR Release with a lot of new features. The Sophos Firewall OS has therefore developed from “good” to “very good” in the last few months. The system is not quite where it should be yet and still has a few shortcomings. But for such a young OS, the progress is very significant!
02 - Hardware
The Sophos XG Firewall hardware and the SG series hardware are identical in terms of CPU, RAM, storage, and ports. A small exception here is the Sophos XG 86 and XG 106, which are not available in the SG series. The two smallest models there would be the SG 85 and SG 105, which have less RAM and storage than the XG 86 and XG 106. But in principle, it is easily possible to install the XG Firewall’s SFOS on SG hardware. The license can then be migrated 1:1.
We have explained how to install SFOS on a Sophos SG Appliance in a KB post: Install Sophos XG Firewall OS on an SG Appliance
A new hardware series is expected next year, which is currently called “XGS”. We cannot say at this point whether this will immediately replace the XG series. In any case, only SFOS is mentioned as a compatible operating system. No new release is planned for the SG series.
What also clearly speaks for an XG Firewall with SFOS, at least at the moment, is support for the new APX Access Points! The Access Points, which were launched back in July 2018 and feature the new Wave 2 standard, are still only compatible with XG Firewalls and Central today. Sophos had always said that the APX Access Points would never be made compatible with the UTM. For us, this step always made perfect sense! This is NextGen hardware, which was developed for NextGen Firewalls.
However, we can now announce, shaking our heads, that Sophos has backed down on this plan. Support for the APX Access Points will come for the UTM! The support is planned for UTM 9.7, which is to be released at the end of the year.
03 - Licensing
The licensing of the XG Firewall is not completely different from that of the UTM. Nevertheless, there are some important advantages.
Base License
The base license for an XG Firewall Appliance is included free of charge. You can find out which functions are included in a separate article about the Base License. Here are the most important functions that you can enjoy free of charge:
- Wireless Protection
- SSL VPN or Sophos Connect Client
- IPsec VPN connections
EnterpriseGuard Bundle
You are certainly familiar with the FullGuard Bundle, which unlocks all modules except Sandstorm on the firewall. With the FullGuard Plus Bundle, you also get Sandstorm.
For the XG series, there is also the popular EnterpriseGuard Bundle. This bundle is a real alternative to the FullGuard Bundle, as it already covers the needs of most customers. With the EnterpriseGuard Bundle, you get Network and Web Protection including Sophos Premium Support. Wireless Protection is already included free of charge in the base license. Thus, only a few customers will have to resort to the more expensive FullGuard Bundle, if there is indeed a need for email and web server protection.
04 - Firewall Rules
Now let’s move on to the more technical part: why, in my opinion, SFOS has the edge over the UTM operating system.
The firewall rule set has become much clearer with SFOS. If you have more than 10 firewall rules, which should be the case in most environments, they can be grouped very effectively in SFOS. The following screenshot of my XG Firewall at home illustrates this again. Here, all IoT devices have their own network, and the firewall rules for them are all grouped together.
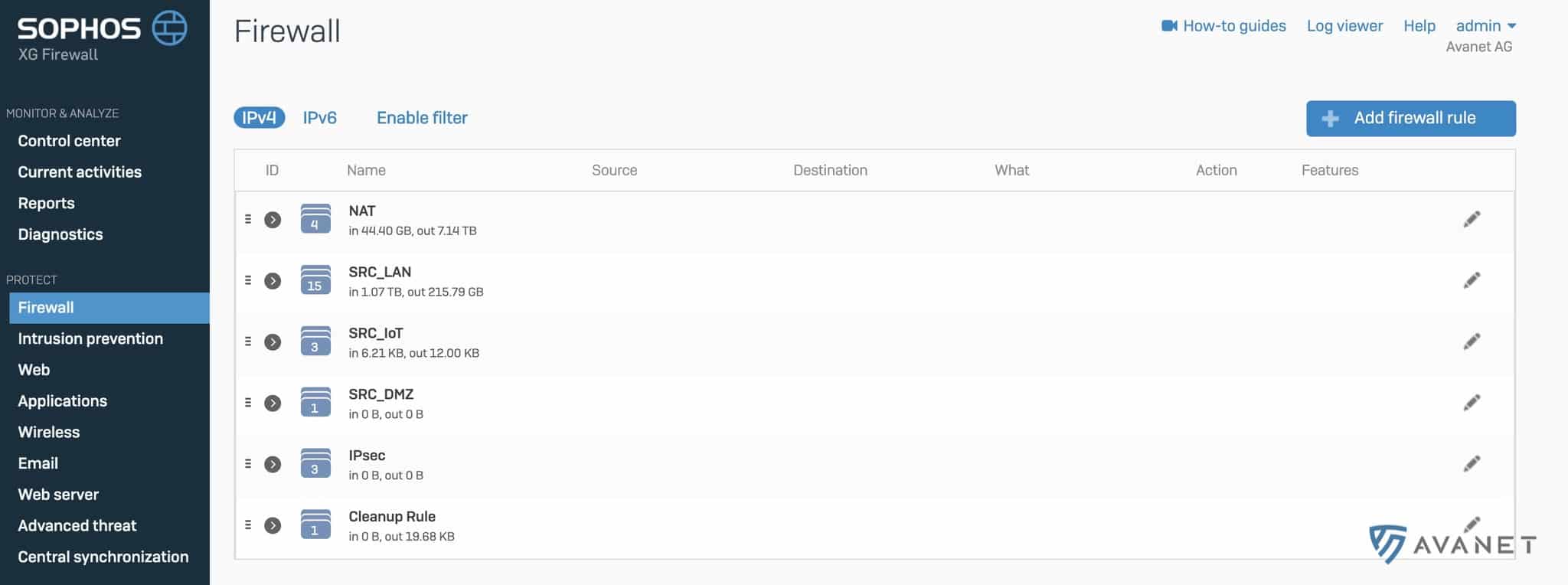
If you then take a closer look at a group, you quickly find out which individual firewall rules still allow traffic through and which rules may no longer be used. This view helps identify and remove unnecessary rules.
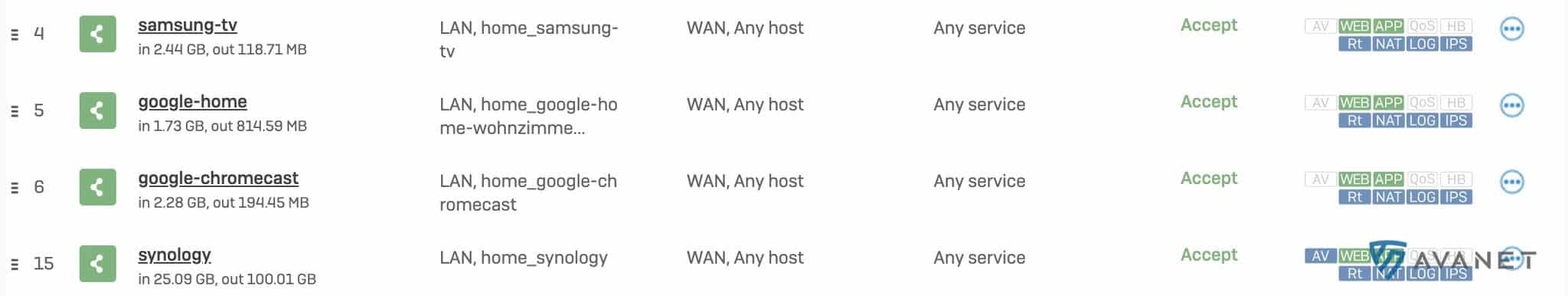
In contrast to UTM, I can give a firewall rule its own name in SFOS. Longer comments are also possible within a rule, for example, to record who created the rule and why it was originally created.
- Each rule gets an ID, with which I can see in the log which traffic passes through this rule.
- You can see at a glance whether, for example, IPS or the web filter is active for a rule.
Regarding firewall rules, I could theoretically list many more advantages that underline why I would never go back to a UTM. But I’ll stick to the main arguments listed above, which should already convince every firewall admin. 🙂
Even if many things have been improved in SFOS regarding firewall rules, SFOS does have a very annoying disadvantage compared to UTM. Saving a firewall rule takes a good 4-10 seconds on XG 86 to XG 135 firewalls! This situation is to be improved first in v18 and then completely resolved in v19.
05 - Log Viewer
Even after several years on the XG Firewall, the Log Viewer is still an absolute highlight! It makes it quick and easy to check logs directly via the GUI. But before I lose too many words about it, just watch the following video:
06 - Sophos Central
No, don’t worry! I’m not going to come up with Sophos Synchronized Security now, from which Sophos’s marketing department has launched a slogan of the century. But if it helps you exchange your UTM for an XG, then we’re happy to jump on the bandwagon, of course. Did you know that with Synchronized Security on the XG Firewall you can see which applications are running on the endpoints? 😂 So yes, Synchronized Security will bring forth even more ingenious possibilities in the future!
But now let’s move on to a Central feature that is still in its infancy but has enormous potential. I am talking about Central Firewall Management. This makes it possible to link the firewall to Central and manage it from there. Such a link can already be created today, but the really interesting functions are yet to come! Unfortunately, I can’t reveal too much here yet, but if Sophos plays its cards right, it could become an SDN management platform. We can already expect new functions by the end of this year.
07 - Firmware Updates
As already said, we always like updates. The saying never change a running system is absolute nonsense when it comes to firewalls. We have already addressed this in an earlier post on the necessity of firewall updates.
You have certainly understood that updates are important. But updates are also risky, as it can happen that not everything runs as smoothly afterwards as before. Admins who are afraid of this are the ones you always hear using the saying mentioned above. 😅
To counteract the danger of updates a little, there are a few improvements on the XG Firewall:
- Updates of Access Points and REDs are decoupled and no longer integrated into the firewall update. This means that REDs can be updated even without restarting the firewall.
- If a firewall update didn’t work and you want to revert to the previous version, this is possible with just a few clicks.
Conclusion
This article has become a bit longer than I originally intended. I have listed seven reasons here that, in my opinion, should encourage every UTM friend to switch. I too once idolized the UTM, but especially in terms of future-proofing, updates, and a clear vision, our common sense suggested the switch to us early on, and we have never regretted it! When it comes to the UTM vs. XG comparison, the XG clearly has the more impressive fighting weight on the scales for us. So be brave or rather sensible (😅) and use an XG Firewall for your next project. Once this step has been taken, you can start migrating your UTMs to SFOS.
Disadvantages
Even if SFOS really offers many excellent features, you might perhaps get the feeling that this article was written through rose-tinted glasses. That is why I am adding a short chapter on the disadvantages here, because as I said, SFOS is still a very young operating system and there are indeed still some things that do not work quite as well as they should.
GUI Speed
- Loading or saving firewall rules still takes too long and does not yet feel the way it should.
- Generating reports or system resources definitely needs a speed boost.
* As already mentioned in the article, these things will be improved with v18 and resolved with v18.5.
Renaming Objects
- Unfortunately, it is not possible everywhere to rename entries after they have been created. This includes, for example, zones, wireless networks, active firewall NAT ports, IPS Protection Policies, Webserver Protection Policies, IPsec Policies and several others.
* The reason for this is that the developers of the Cyberoam Firewall, which is still the basis for SFOS, used the name for these objects as the primary key in the database. This naturally makes renaming afterwards rather difficult. But work is being done on this as well, and initial improvements are expected with v18.
NAT Rules
- Created NAT rules can no longer be edited if they are active. They must first be deactivated, edited, and then reactivated.
* To be fixed with v18.
Notifications
- Notifications are still worlds better on the UTM system. There, you can practically be notified of everything via email. SFOS offers almost no options in this regard. With SFOS 17.5 MR4, some improvements were made in this regard, but these possibilities that we took for granted with the UTM are still far from being offered.
* To be further improved with v18.
More Information
In this article, I often refer to v18, which is supposed to bring many improvements. According to Sophos, v18 is expected to be released by the end of 2019. However, we consider this timeline to be very optimistic and consider Q1 2020 to be a more accurate release period. 😅

