Sophos Central Intercept X Advanced for servers with XDR
207.70 CHF - 454.85 CHF
| Quantity | Unit price |
|---|---|
| 1 - 9 | 207.70 CHF |
| 10 - 24 | 151.75 CHF |
| 25 - 49 | 144.87 CHF |
| 50 - 99 | 133.88 CHF |
| 100 + | 127.47 CHF |
Description
Get to the bottom of the cause of attacks!
Technical Specifications
Compare the range of functions of the different Server from Sophos to protect your infrastructure. Not sure which protection best suits your business? We can advise you free of charge and without any obligation.
| Multiple guidelines | - | ✔ | ✔ | ✔ | ✔ |
| Controlled updates | - | ✔ | ✔ | ✔ | ✔ |
| Web Security | ✔ | ✔ | ✔ | ✔ | ✔ |
| Download reputation | ✔ | ✔ | ✔ | ✔ | ✔ |
| Web Control/Category-based URL Blocking | - | ✔ | ✔ | ✔ | ✔ |
| Peripheral control | - | ✔ | ✔ | ✔ | ✔ |
| Application Control | - | ✔ | ✔ | ✔ | ✔ |
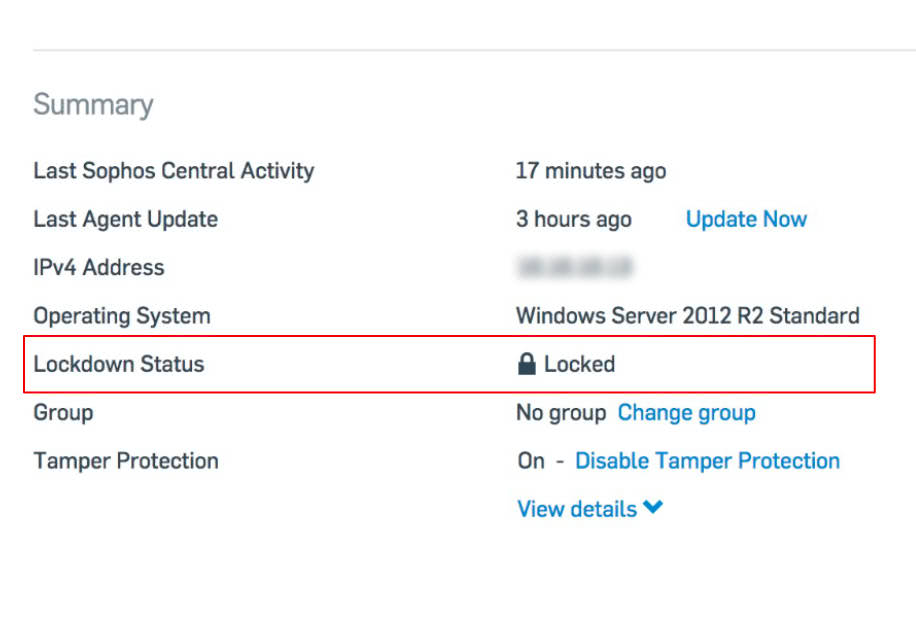
| Application Whitelisting (Server Lockdown) | - | ✔ | ✔ | ✔ | ✔ |
| Deep Learning Malware Detection | ✔ | ✔ | ✔ | ✔ | ✔ |
| Anti-malware file scans | ✔ | ✔ | ✔ | ✔ | ✔ |
| Live Protection | ✔ | ✔ | ✔ | ✔ | ✔ |
| Behavioral analysis before execution (HIPS) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Blocking potent. Unwanted applications (PUAs) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Intrusion Prevention System | ✔ | ✔ | ✔ | ✔ | ✔ |
| Data Loss Prevention | ✔ | ✔ | ✔ | ✔ | ✔ |
| Runtime behavior analysis (HIPS) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Antimalware Scan Interface (AMSI) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Malicious Traffic Detection (MTD) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Exploit Prevention | ✔ | ✔ | ✔ | ✔ | ✔ |
| Active Adversary Mitigations | ✔ | ✔ | ✔ | ✔ | ✔ |
| Ransomware File Protection (CryptoGuard) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Disk and Boot Record Protection (WipeGuard) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Man-in-the-Browser Protection (Safe Browsing) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Enhanced Application Lockdown | ✔ | ✔ | ✔ | ✔ | ✔ |
| Live Discover (cross-environmental SQL queries for threat hunting and security compliance) | - | - | ✔ | ✔ | ✔ |
| SQL query library (pre-formulated, customizable queries) | - | - | ✔ | ✔ | ✔ |
| Suspicious event detection and prioritization | - | - | ✔ | ✔ | ✔ |
| Data storage on hard disk (up to 90 days) with fast data access | - | - | ✔ | ✔ | ✔ |
| Cross-product data sources (e.g. firewall, e-mail) | - | - | ✔ | ✔ | ✔ |
| Cross-product queries | - | - | ✔ | ✔ | ✔ |
| Sophos Data Lake (cloud data storage) | - | - | 30 days | 30 days | 30 days |
| Scheduled queries | - | - | ✔ | ✔ | ✔ |
| Threat cases (root cause analysis) | - | ✔ | ✔ | ✔ | ✔ |
| Deep Learning Malware Analysis | - | - | ✔ | ✔ | ✔ |
| Advanced threat data from SophosLabs on demand | - | - | ✔ | ✔ | ✔ |
| Export of forensic data | - | - | ✔ | ✔ | ✔ |
| Automated malware removal | ✔ | ✔ | ✔ | ✔ | ✔ |
| Synchronized Security Heartbeat | ✔ | ✔ | ✔ | ✔ | ✔ |
| Sophos Clean | ✔ | ✔ | ✔ | ✔ | ✔ |
| Remote terminal access (remote analysis and response) | - | - | ✔ | ✔ | ✔ |
| On-demand server isolation | - | - | ✔ | ✔ | ✔ |
| With one click "Remove and block | - | - | ✔ | ✔ | ✔ |
| Cloud Workload Protection (Amazon Web Services, Microsoft Azure, Google Cloud Platform) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Synchronized Application Control (transparency over applications) | ✔ | ✔ | ✔ | ✔ | ✔ |
| Management of your security status in the cloud (cloud hosts monitor and protect, serverless functions, S3 buckets, etc.). | - | ✔ | ✔ | ✔ | ✔ |
| Server-specific policy management | ✔ | ✔ | ✔ | ✔ | ✔ |
| Update cache and message relay | ✔ | ✔ | ✔ | ✔ | ✔ |
| Automatic scan exceptions | ✔ | ✔ | ✔ | ✔ | ✔ |
| File Integrity Monitoring | - | - | ✔ | ✔ | ✔ |
| 24/7 evidence-based threat hunting | - | - | - | ✔ | ✔ |
| Compatible with third-party security tools | - | - | - | ✔ | ✔ |
| Security Health Checks | - | - | - | ✔ | ✔ |
| Activity Reports | - | - | - | ✔ | ✔ |
| Sophos MDR ThreatCast | - | - | - | ✔ | ✔ |
| Attack detection | - | - | - | ✔ | ✔ |
| Stop and contain threats | - | - | - | ✔ | ✔ |
| Direct telephone support for incidents | - | - | - | ✔ | ✔ |
| 24/7 circumstantial threat hunting | - | - | - | - | ✔ |
| Proactive Security Posture Improvement | - | - | - | - | ✔ |
| Full incident response: complete neutralization of Threats | - | - | - | - | ✔ |
| Root cause analysis – and how can renewed attacks be prevented? | - | - | - | - | ✔ |
| Dedicated contact person at the Incident Response Team | - | - | - | - | ✔ |
Avanet Services
Let us improve your safety
Our services are designed to help you keep your Sophos products running securely and reliably. In addition to the classic support for Sophos Firewalls or the Central platform, we offer the following services, which can be requested from us at any time:
Setup Services
Health Check
Upgrades
Workshops
Migrations
Firewall maintenance
SLA
Security audits
Request more informationSetup Services
Want to have your Sophos products set up by professionals? We support you during commissioning and configuration for smooth operation.
Migrations
You would like to change from your SG Firewall (UTM) to a XGS Firewall with the SFOS operating system? Thanks to our experience, we can also manage your changeover without any worries.
Health Check
You have set up your Sophos products yourself and would like us to check the configuration? We will check your settings and give our recommendation.
Workshops
Is it your job to be knowledgeable about Sophos products in your organization? We offer targeted training that is completely tailored to your needs.
Resources
Deepen your knowledge and learn more about “Sophos Central Server Protection”
Sophos Managed Detection and Response (MDR) – Datasheet
Sophos Managed Detection and Response (MDR) – Buyer's Guide
Sophos Breach Protection Warranty – Datasheet
Sophos Rapid Response – Datasheet
Extended Detection and Response (XDR) – Beginner’s Guide
Sophos Network Detection and Response (NDR) – Datasheet
Sophos Network Detection and Response (NDR) – Solution Brief
Sophos Server Protection – Buyer's Guide
Cybersecurity System – Buyer's Guide
Sophos Intercept X for Server – Datasheet
Sophos Intercept X – Solution Brief
Sophos Intercept X Deep Learning
FAQs zu Intercept X Essentials und Intercept X Essentials for Server
EDUCATION & GOVERNMENT
Special awards for educational and government institutions
Sophos offers special discounts for schools and government institutions to meet specific budget requirements. A discount of at least 20 % can be expected.*
Ask us and we will prepare an offer for you completely free of charge and without obligation.
* Special pricing for educational and government institutions is only available in the DACH region.
Request special pricesTrial version
Try Sophos Central for free
Try out the powerful platform for centralized security management free of charge for 30 days.
All products - Test the complete protection package, including XDR protection for endpoints, email, mobile devices and servers.
One console - work efficiently by managing all Sophos products from a single cloud platform.
Immediate access - ready for use in just a few minutes.
Use the following login details to start your online demo. Username: demo@sophos.com / Password: Demo@sophos.com
Help with purchase
Are there any questions about the product?
It is better to ask again before buying, before you end up holding the wrong product in your hands.
Ask question| Laufzeit | 1 year, 2 years, 3 years |
|---|---|
| Art | Initial purchase, Renew |