Sophos SFOS v18 - New Features at a Glance
Sophos Firewalls running SFOS will soon receive another major update with SFOS v18. We are already using the beta in production. In this article, you will learn which features the new version brings and how it performs in everyday use.
Live Production Testing
We are not testing the beta on an isolated test appliance in a lab environment, but directly in production. Selected customers with more than 650 users are also using the version so that we can gather the broadest possible insights into the new release. In this post, we are therefore not simply repeating content from Sophos’ official information material, but reporting on SFOS v18 EAP1 and EAP2 based on several weeks of practical experience. This article is correspondingly detailed because we look at many features closely. Let us start with the Xstream architecture.
Xstream Architecture
A particular highlight of v18 is the new packet processing architecture. It delivers more performance, greater security, and significantly better visibility into encrypted traffic. A great deal has changed in this area with v18.
Info: The “X” in “Xstream” stands for Next Generation, and “Stream” refers to the new DPI Engine, a streaming-based scanning solution.
Xstream SSL/TLS Inspection
We have already written about SSL Inspection, often also called “SSL scanning” or “HTTPS scanning”: HTTPS Scanning: Why it should be enabled on Sophos
In short: The firewall can inspect HTTP traffic without any problem because it is unencrypted. HTTPS traffic, on the other hand, first has to be broken open before the firewall can analyze it. Until now, the problem was that the web proxy could only decrypt HTTPS traffic running on port 443. If the traffic used another port, for example https://www.example.com:8000, the firewall remained blind.
With v18, the firewall is ready again for current technologies and can inspect both SSL and TLS 1.3 traffic, regardless of which ports or protocols the traffic uses. 🤩 Under the hood, this required extensive architectural changes, which fortunately do not create extra work for administrators.
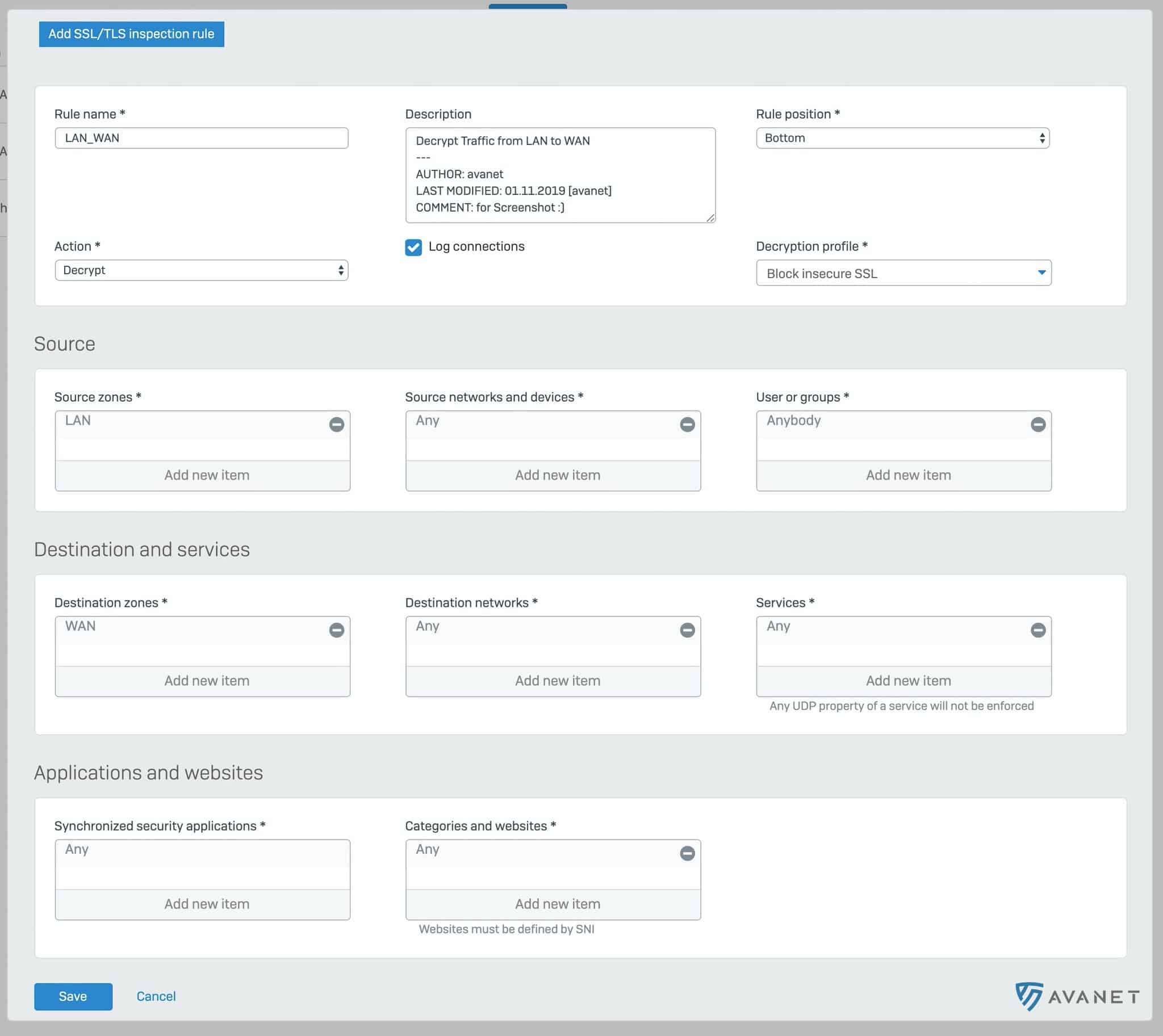
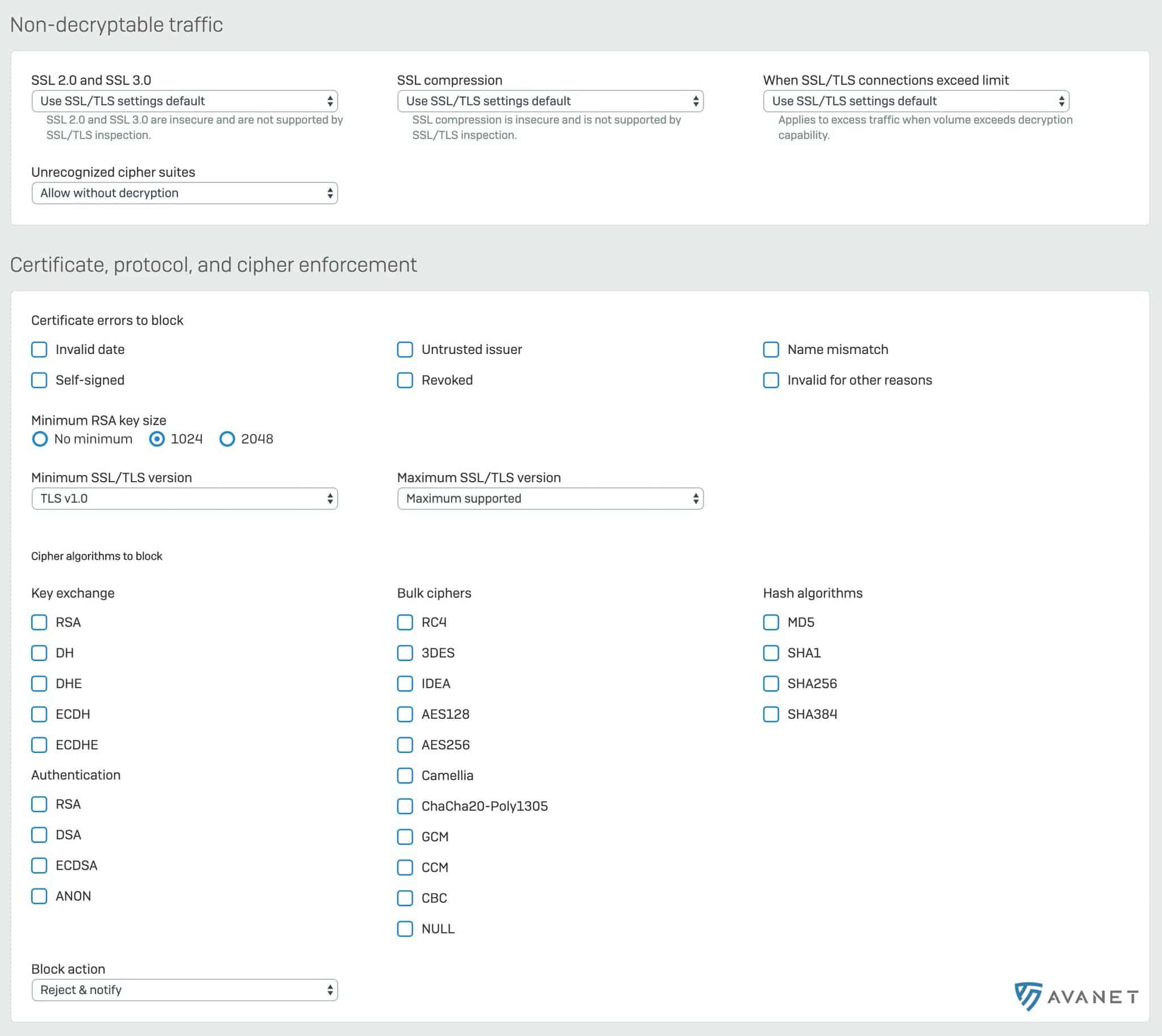
The central elements are a Decryption Profile, which is linked to an SSL/TLS Inspection Rule. This rule defines which traffic should be inspected.
The DPI Engine can then take over tasks such as Advanced Threat Protection, App Control, and IPS.
It is important to understand that the new DPI Engine is in direct competition with the existing Web Proxy. The Web Proxy is responsible for HTTP/HTTPS traffic, web policies, and content scanning; the new DPI Engine can alternatively take over these tasks.
When upgrading from version 17.5 to 18.0, the web proxy settings are carried over. Anyone who wants to use the DPI Engine, however, has to make a few adjustments: an SSL/TLS Inspection Rule is configured and the Web Proxy is disabled in the firewall settings.
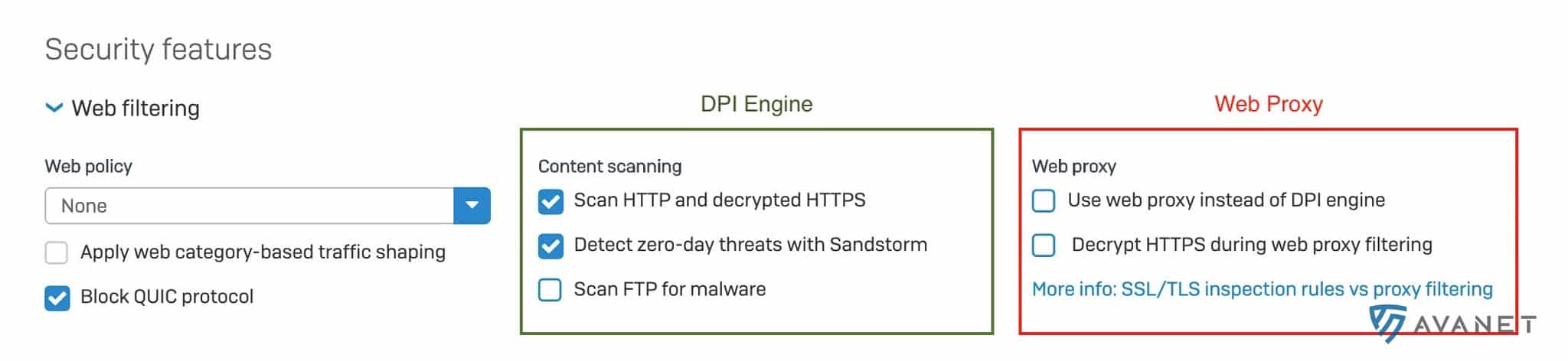
There are only a few reasons not to use the new DPI Engine. Nevertheless, the Web Proxy offers some functions that are not yet available in the DPI Engine, including SafeSearch for search engines or YouTube, Caching, and Pharming Protection. On all firewalls we manage, however, we can easily do without these additional functions, which is why we will certainly use the DPI Engine.
The following Sophos video gives you a compact introduction to the Xstream DPI Engine and helps you decide when to use the DPI Engine compared with the classic Web Proxy:
Xstream Network Flow FastPath
Many administrators know the problem of the firewall noticeably slowing down traffic and making certain processes feel slower. The new architecture now introduces the so-called FastPath. It allows the firewall to offload non-critical traffic directly to the kernel and thus significantly increase performance.
Traffic first passes through the Firewall Stack. There it is checked whether a matching firewall rule exists and whether the traffic is allowed at all. If, for example, the traffic is inspected by IPS, it first passes through the DPI Engine. As soon as the IPS engine classifies the traffic as harmless, it can be offloaded to the FastPath and forwarded directly via the kernel.
Looking at the architecture diagram naturally raises the question of how this works in practice. It is relatively quick to determine whether traffic is generally allowed; this step does not have to be repeated for every packet from the same source and port. But how does the DPI Engine know when traffic can be moved to the FastPath? If SSL/TLS scanning is enabled, for example, this is not possible because the traffic would otherwise no longer be inspected. With IPS or application control, however, known lists are used as the basis for deciding whether a data stream is considered harmless.
Threat Intelligence Analysis
If the Sophos Sandstorm module is licensed for the firewall, files are already checked in a sandbox before they are downloaded. Anyone who wants to learn more about Sophos Sandstorm can look at the Sophos Sandstorm PDF with FAQs. Thanks to SSL/TLS Inspection, the firewall gains deeper insight into traffic and can control web downloads even more precisely. Endpoint protection also remains in place as the final layer of defense.
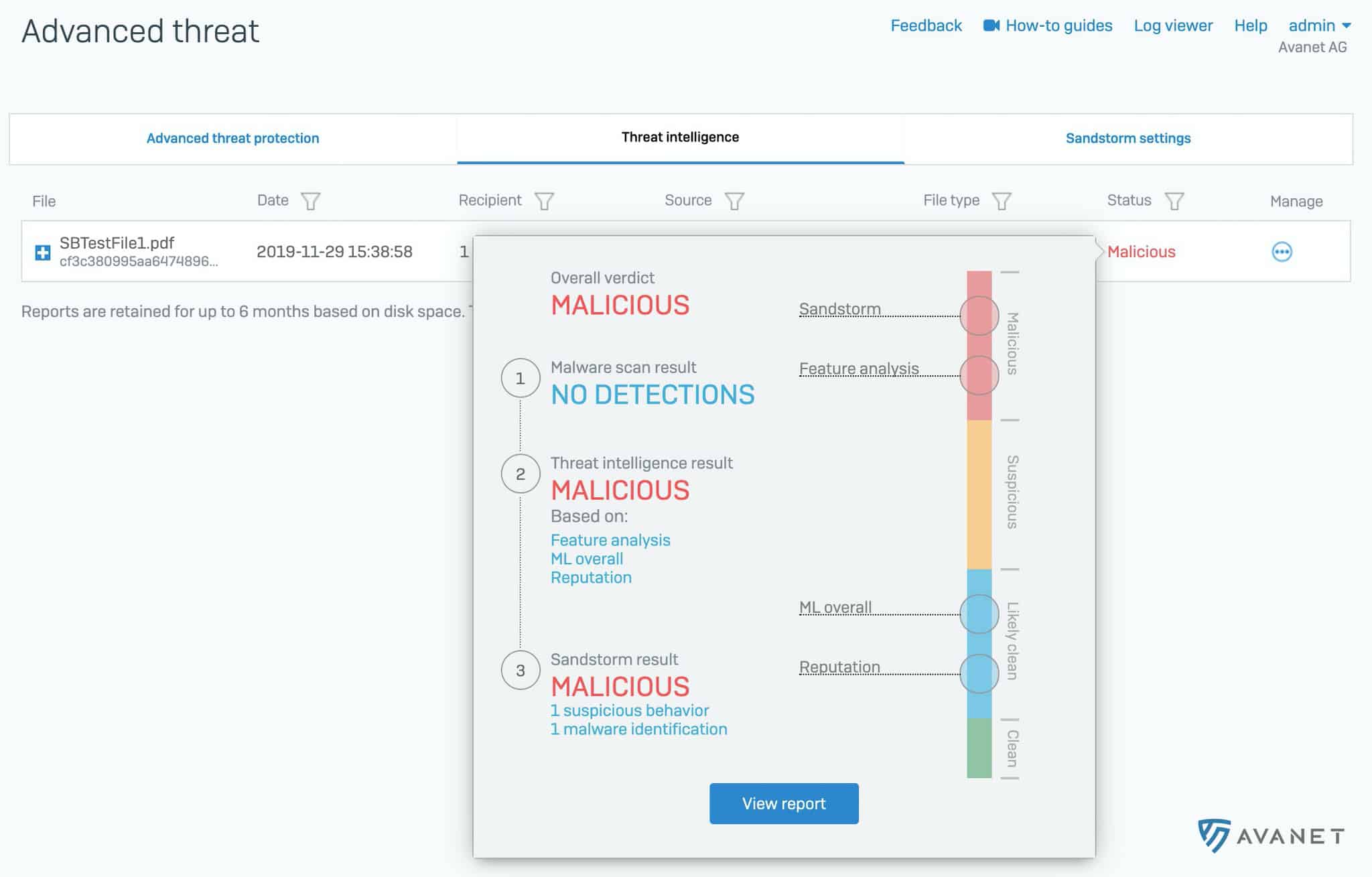
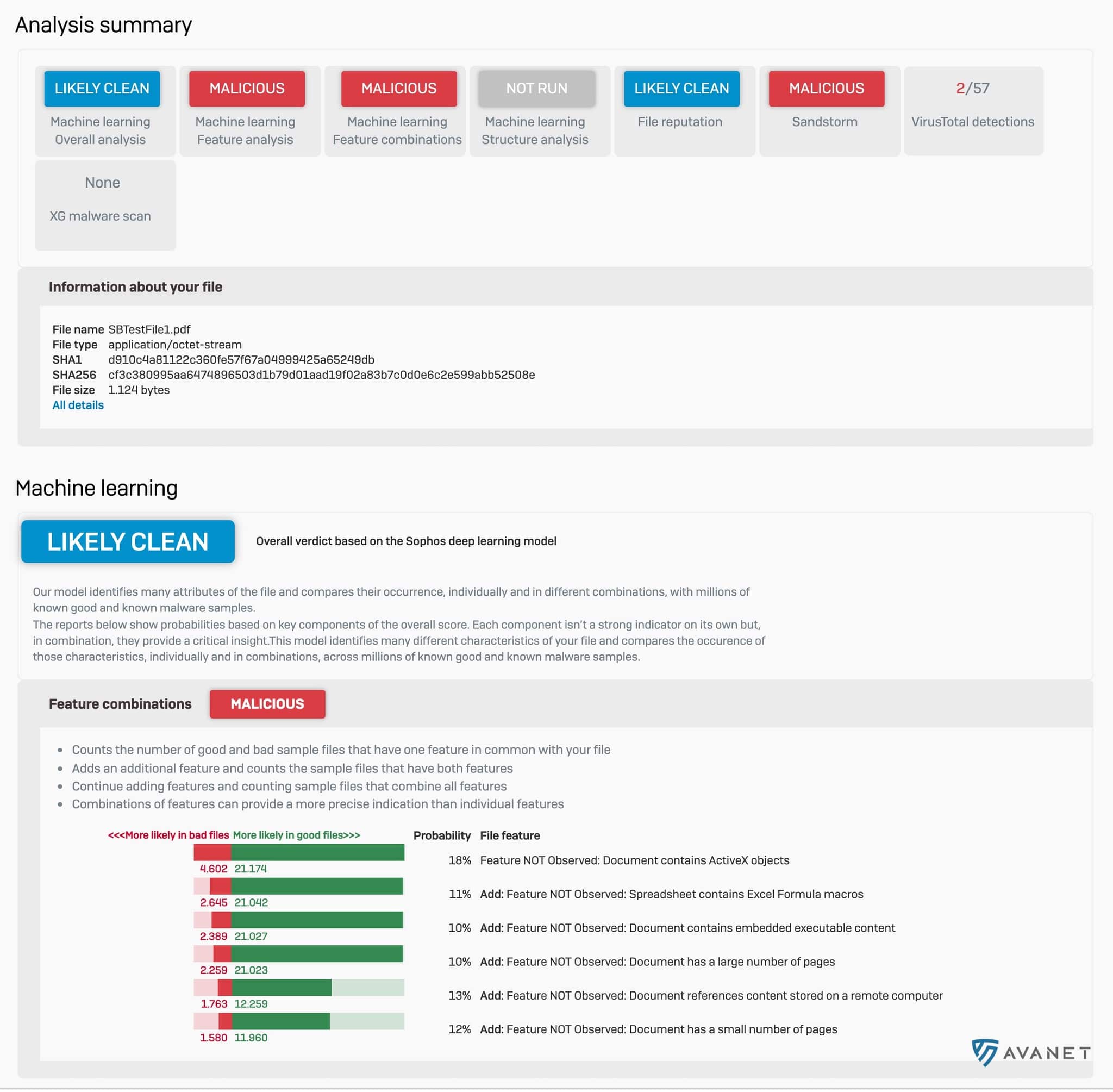
With v18, the new Threat Intelligence Analysis complements the existing Sandstorm module. While Sophos Sandstorm analyzes web downloads or email attachments, Threat Intelligence checks files using machine learning. It also uses SophosLabs analysis, the same analysis used by Sophos Intercept X with EDR.
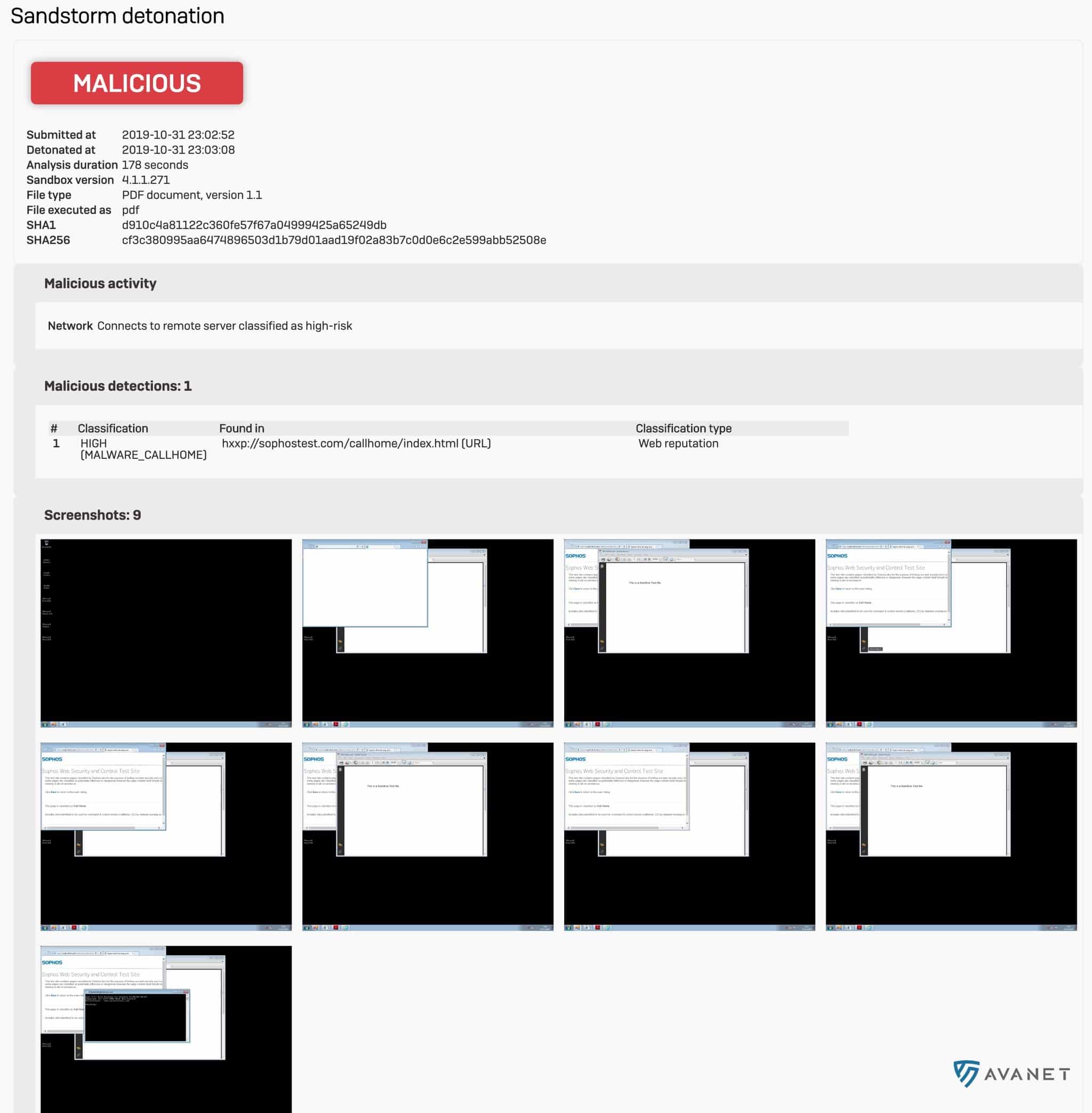
As with EDR, a detailed analysis report is created. In SFOS v18 EAP2, such a report looks like this, for example:
The slightly nicer report is only available from EAP3 onward.
Enterprise NAT
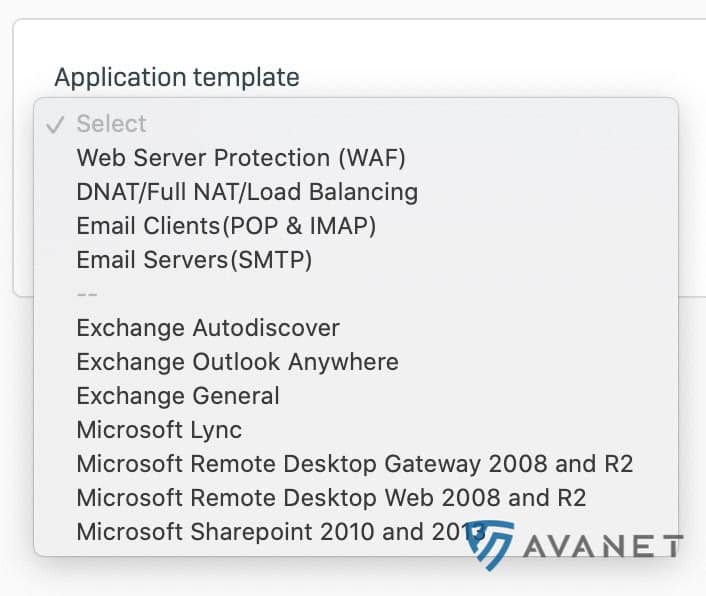
In addition to the Xstream architecture, the NAT rules have also been fundamentally redesigned. Up to version 17.5, there was a “Firewall” menu item under which all firewall rules, NAT rules, and WAF rules were grouped. In a firewall rule, you could define, among other things, the outgoing interface or outgoing IP for the traffic.
With v18, NAT rules are managed in their own tab, making management much more flexible.

Many customers have been waiting for this change: for example, all DNS or NTP requests to public servers can now be blocked and redirected to an internal server instead. This also provides a solution for anyone who misses the NTP server on the XG that was still built into the UTM.
NAT is also explained in the following video:
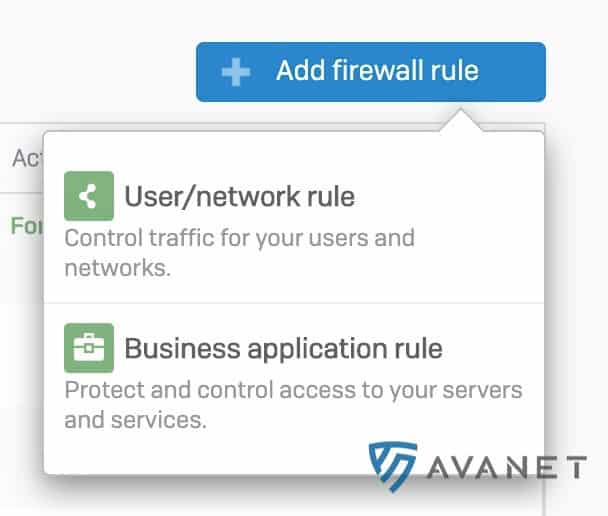
Firewall Rule Management
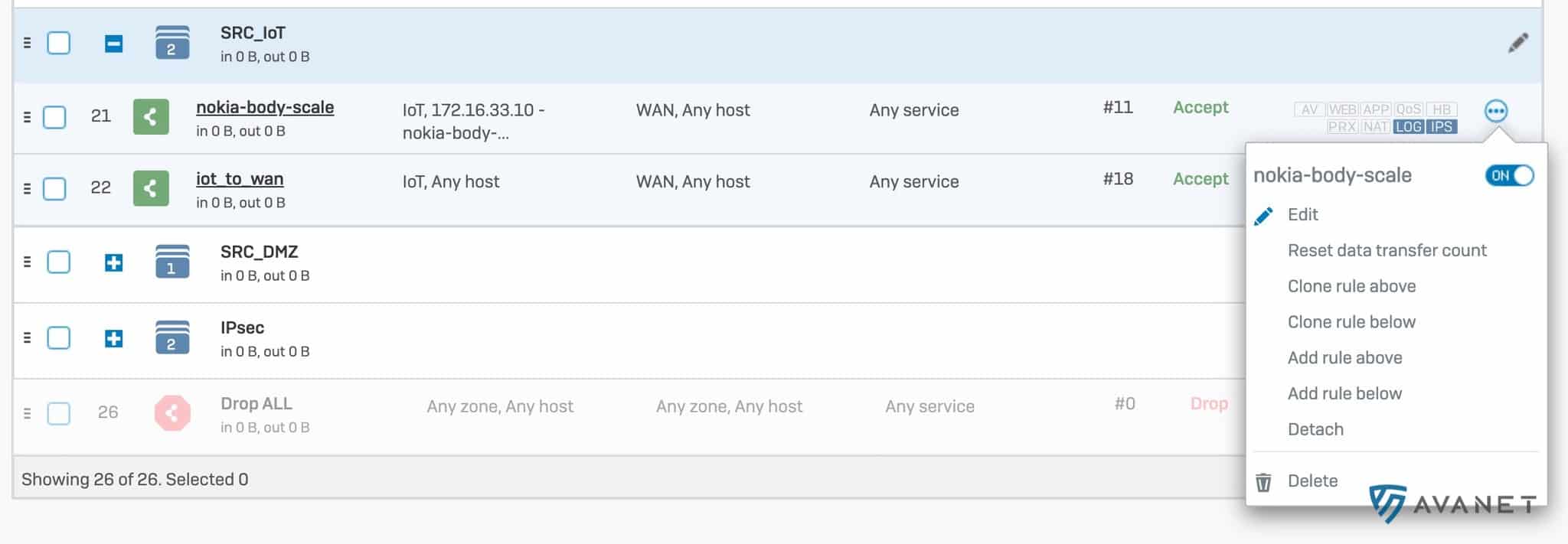
With every new major version, Sophos improves the handling of firewall rules. In v18, multiple firewall rules can now be selected at the same time in order to delete, enable, or disable them, or to add them to or remove them from a group. Firewall rules are also now numbered, so the total number is immediately visible. The rule ID remains unchanged. The “Firewall” menu item has also been renamed “Rules and policies”.
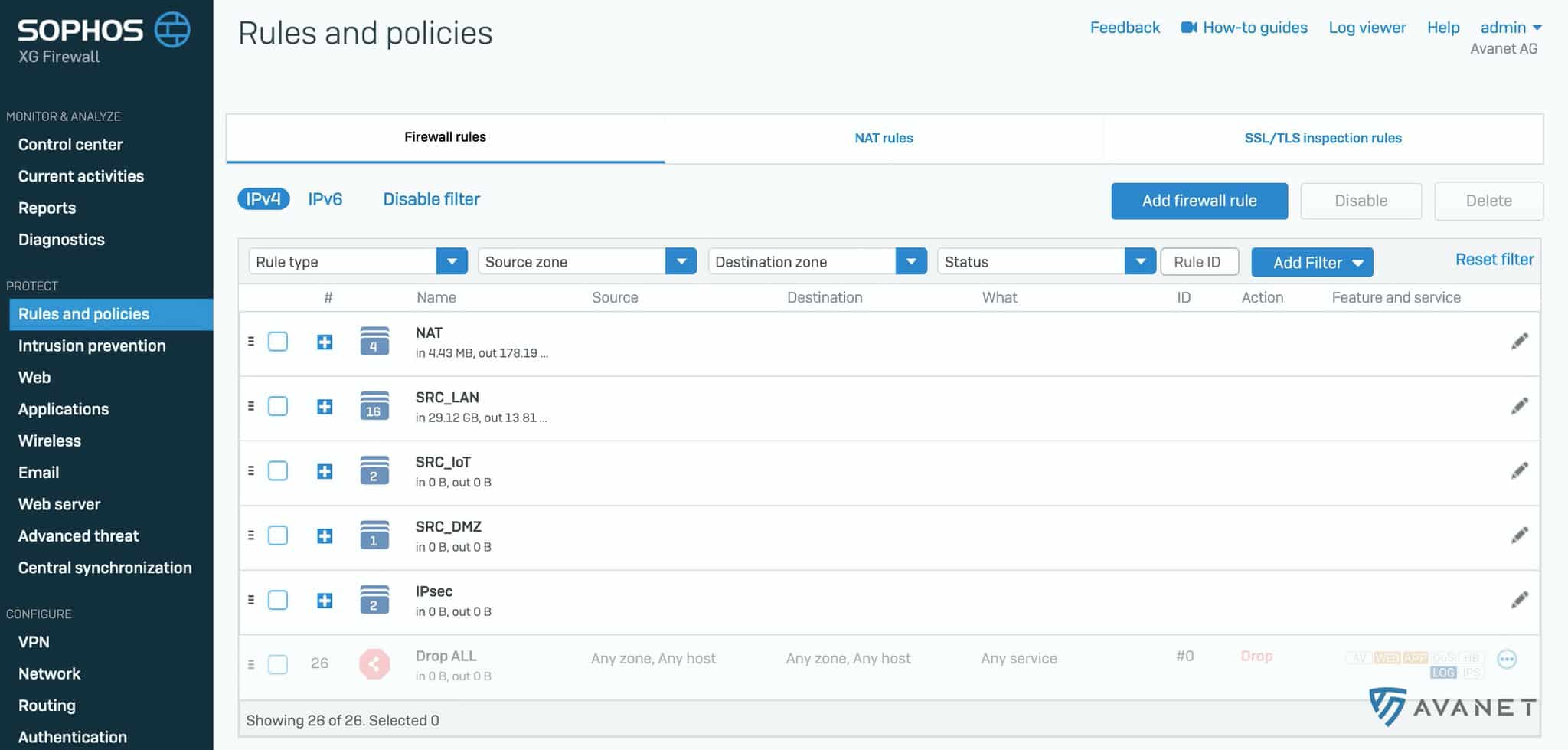
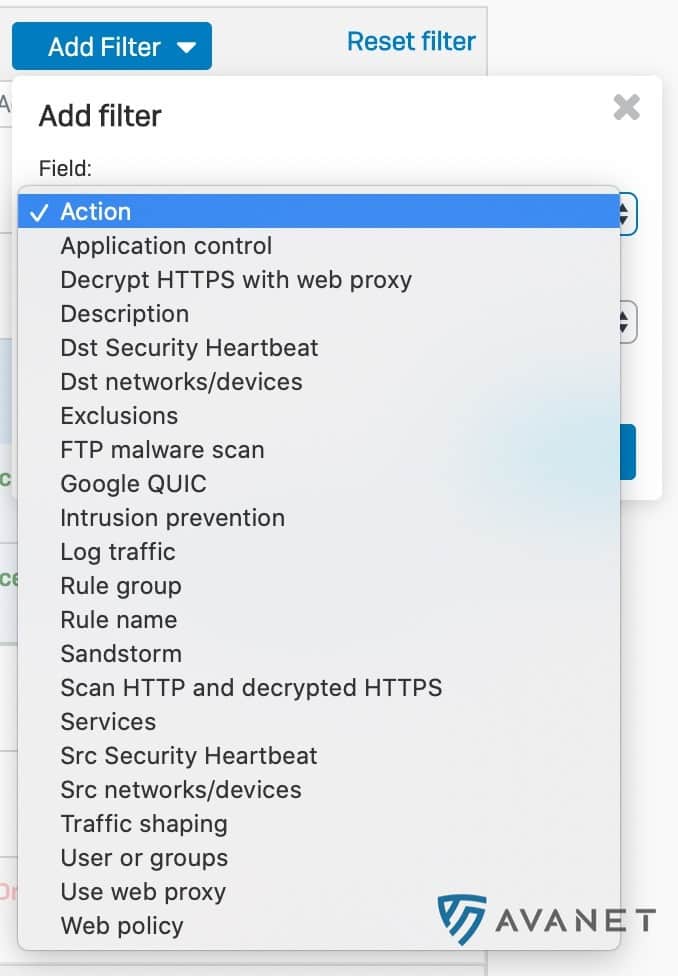
Filters can now be set, which makes searching for specific rules much easier. The filter is retained even if you switch between menu items and then return to the ruleset.
Anyone who hoped that Sophos would now also leave rule groups open after saving a rule will unfortunately be disappointed. Nothing has changed here. 😖
A frequently requested function has also been added: the counter for traffic processed by a firewall rule can be reset to zero again.
When creating a new firewall rule, it is now possible to create the rule in a disabled state first.
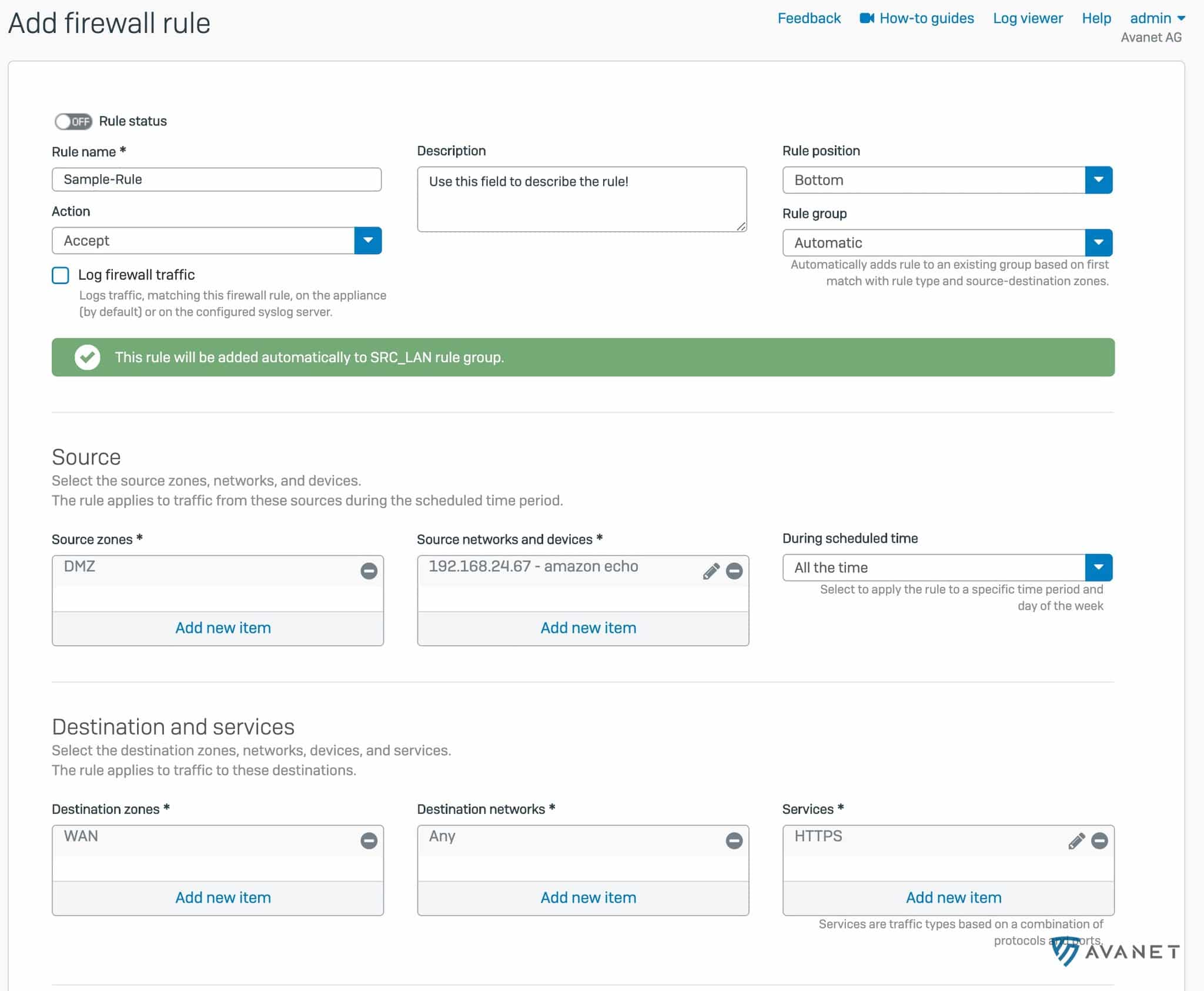
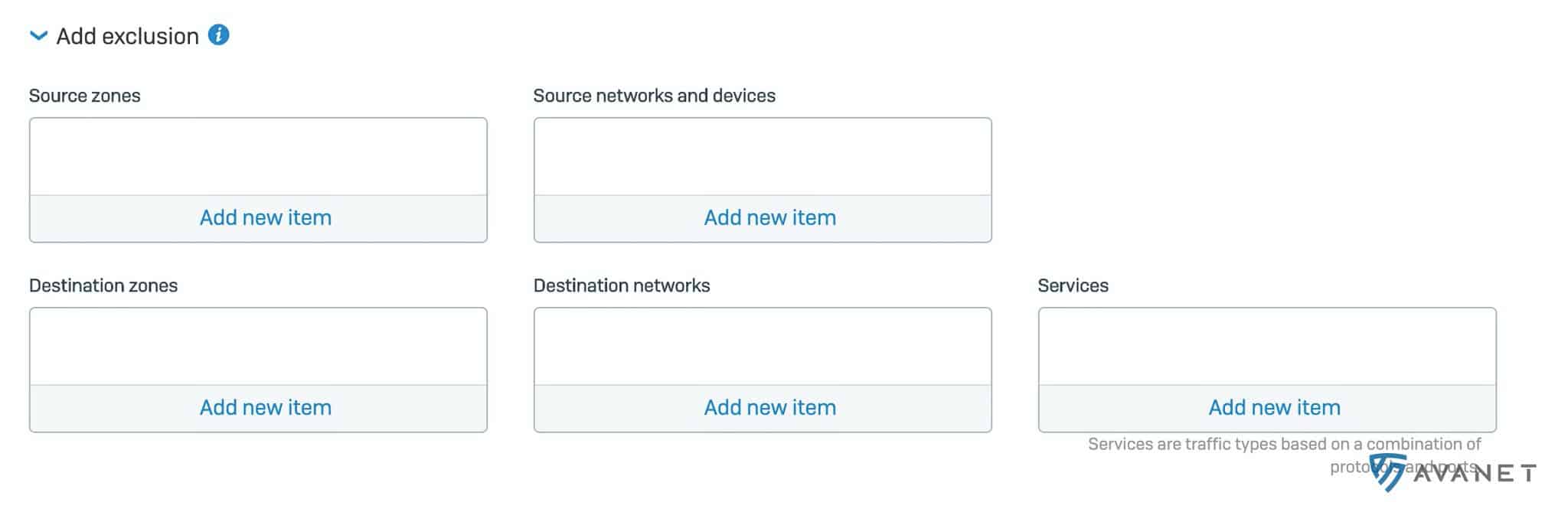
Exclusions can also now be defined in firewall rules. This helps keep the ruleset lean and avoids unnecessary additional rules.
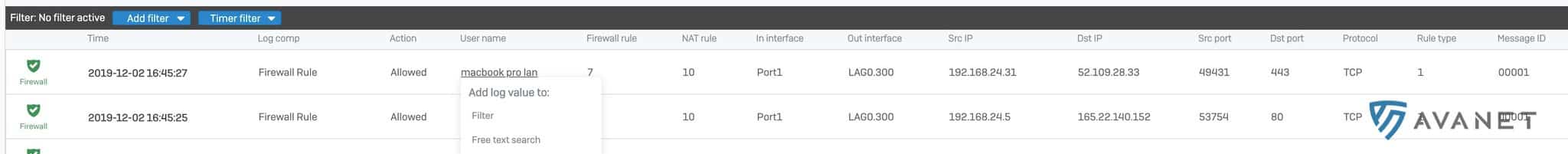
Log Viewer
Anyone who has read the article 7 reasons why the XG Firewall (SFOS) is better than the UTM knows how useful the Log Viewer is. In the new version, the tool gains a few helpful new functions.
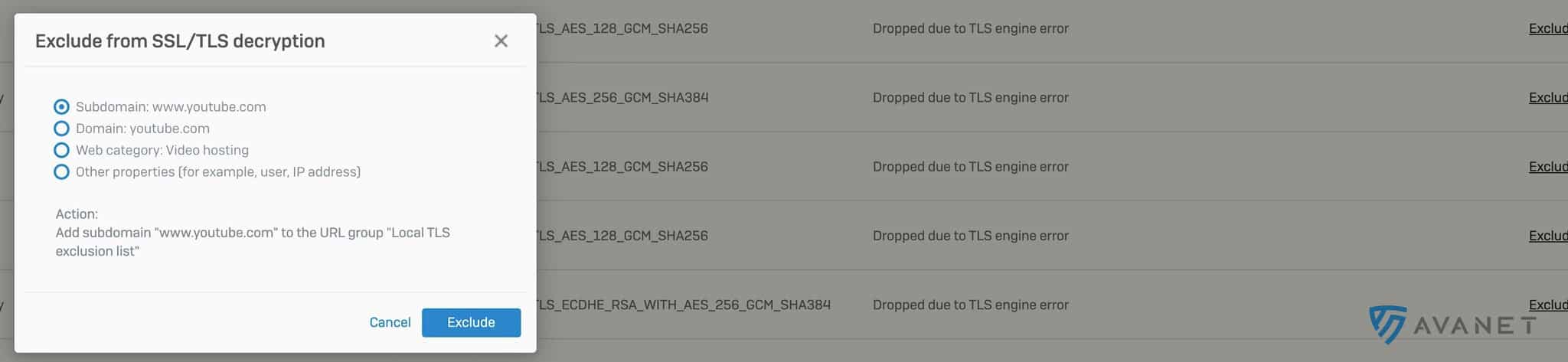
With one click on an entry in the Log Viewer, you can directly set a filter, define an SSL/TLS exception, or adjust an IPS, Application Control, or web filter policy.
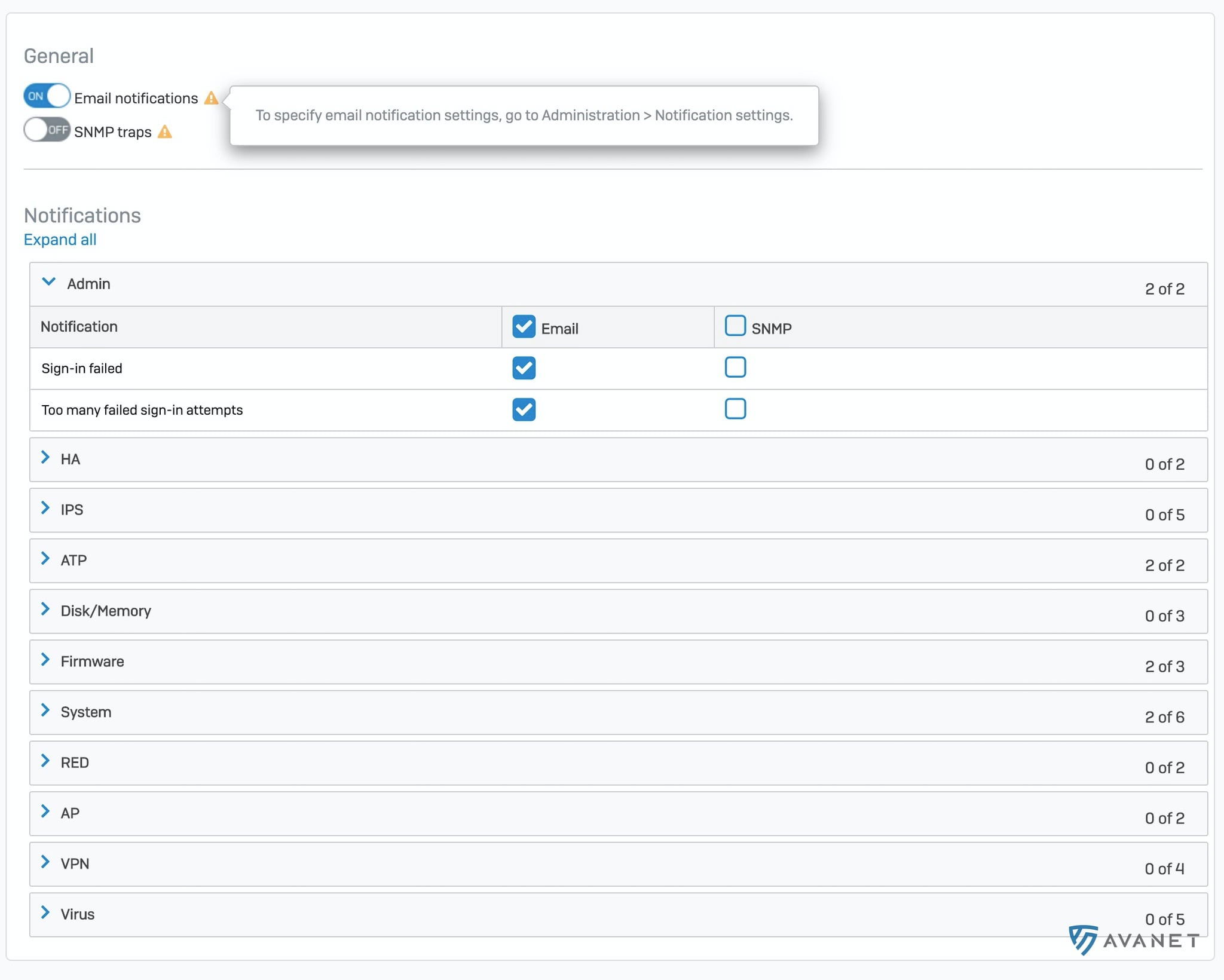
Alerts and Notifications
Under “Administration” > “Notification settings”, only two options for email notifications could previously be enabled:
- IPsec tunnel up/down
- Email alert notifications
If a RED was unreachable or a user entered the wrong password too often, there was previously no way to be notified.
Improvements: Appliances can now be combined into a cluster faster and more easily. Firmware rollback is also possible.
- SNMPv3 support: Significantly better security compared with SNMPv1 and SNMPv2, assuming the first two versions could be called “secure” at all. The MIB File is available for download as usual.
- Renaming interfaces: Until now, interfaces were named Port1, Port2, and so on, without any way to change this. In v18, these names can now be adjusted. IPsec, IPS, wireless networks, and so on still cannot be renamed.
- GeoIP database updates: The country IP database can now be updated independently of firmware updates.
- VMware Tools upgrade: VMware Tools are now available in version v10.3.10 and also support Site Recovery Manager (SRM).
Upgrade to SFOS v18
Requirements
Curious about upgrading to v18? If you already use an XG Firewall or an SG with SFOS, you need at least version v17.5 MR6 to move to v18. As usual, rollback is supported. If something does not work as expected with v18, you can always return to the previous version.
SG to XG
If you are still using a UTM firewall, you can also switch to SFOS. You can find the relevant guide here: Install Sophos XG Firewall OS on an SG appliance
If you need support with the migration, we will be happy to help. We have already successfully replaced numerous UTM systems. 😎
XG 85 and XG 105
At least 4GB RAM is required to install v18. The upcoming SFOS version will therefore no longer run on an XG 85 or XG 105. Anyone using their own hardware with only 2GB RAM installed faces the same problem. Cyberoam will also no longer be supported.
Owners of an XG 85 or XG 105 should take a look at the successor models: Sophos XG 86 and XG 106. Sophos is currently running a promotion until 30.09.2020 that lets you save 50% on the new hardware when renewing.
Sophos Central Firewall Reporting and Management
There is a separate blog post on this topic: Sophos Central Firewall Management - Features with SFOS v18