Sophos XG update v17.5 - All new features at a glance
We installed the second beta of the new SFOS 17.5 firmware at the beginning of November and took a closer look. At the Sophos Roadshow in March 2018 in Dübendorf, there was still talk of versions 17.2 and 17.3, but Sophos decided to bundle all planned features and jump straight to version 17.5.
One thing we can say upfront: SFOS 17.5 leaves us with somewhat mixed feelings. There are some cool new features, but from our point of view, they are not always fully thought through.
Lateral Movement Protection
Since the first version of Synchronized Security, the endpoint client has been able to share its status with the firewall. Thanks to this feature, we can, for example, deny a workstation that has not received updates for a long time, or is already infected, access to the file server or the internet so that other systems are not put at risk.
Up until now, such a configuration required good network segmentation. If all devices in a company are connected to the same switch and are in the same network, Security Heartbeat has not really had much effect so far.
With SFOS 17.5, this feature has been expanded and improved. It is now also possible to isolate computers that Synchronized Security has classified as “unhealthy” from other computers in the same broadcast domain or network. When there is a problem with a client, the firewall automatically informs all the other clients. This means that not only the firewall knows when something is wrong with a client, but all other clients in the network as well. This allows an infected device to be isolated even more effectively until the problem has been resolved. As soon as the Security Heartbeat status switches back to “green”, the connections to other systems in the network are automatically restored.
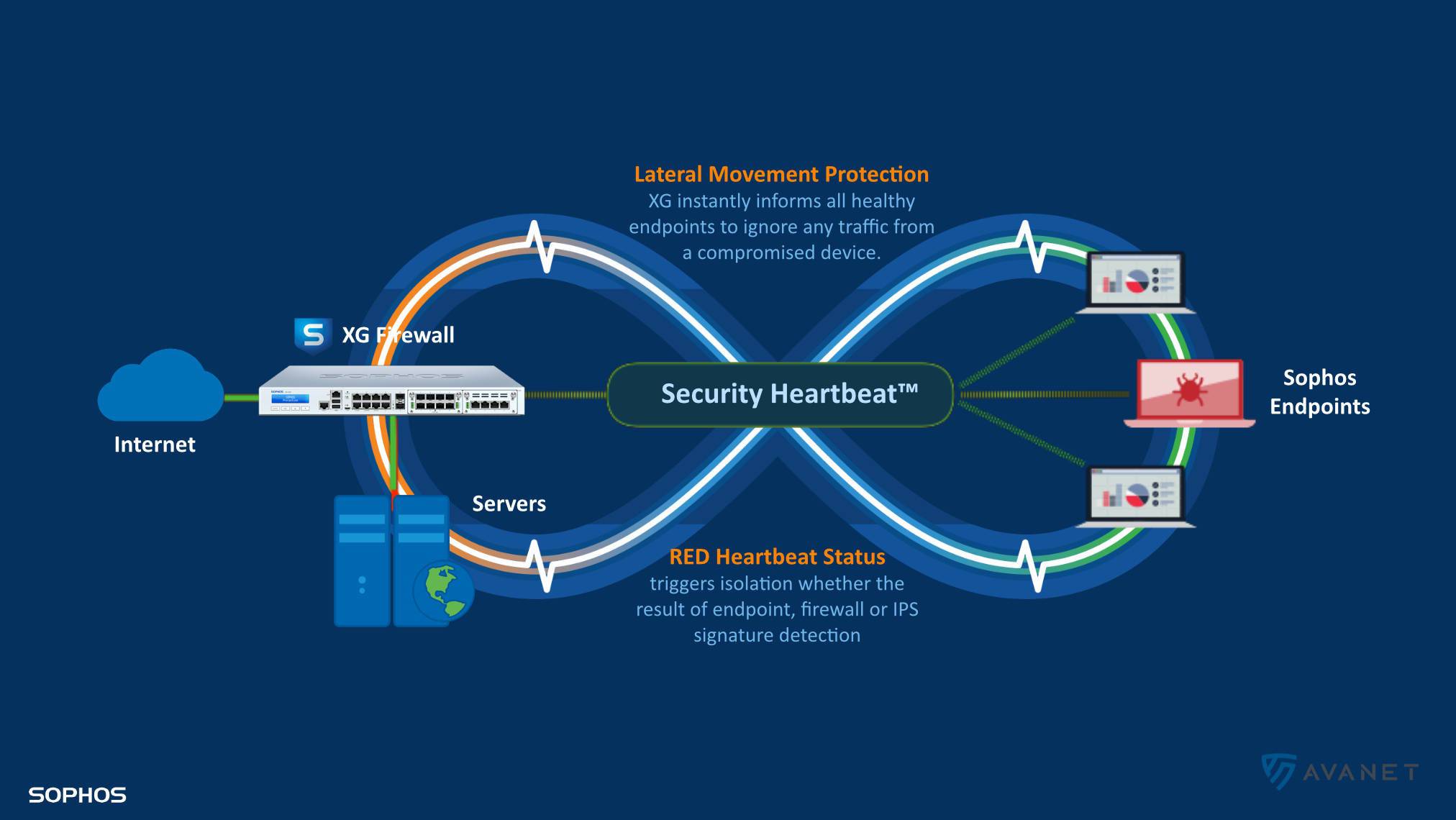
Additionally, IPS detections from compromised endpoints can now also trigger a “red” heartbeat. This further improves protection against threats on the network.
Forwarding portal URL
During my tests, I noticed a function that was almost quietly introduced into the new version, as it is not mentioned anywhere in the release notes.
You all know the situation: when a website is blocked by the Sophos web proxy, a warning page is displayed to the user. If the user then wants to access the page anyway, the link behind it used to contain an IP address instead of a normal URL. In version 17.1, you could at least change this via the console. With 17.5, this is now conveniently possible via the XG Firewall web interface. 👍
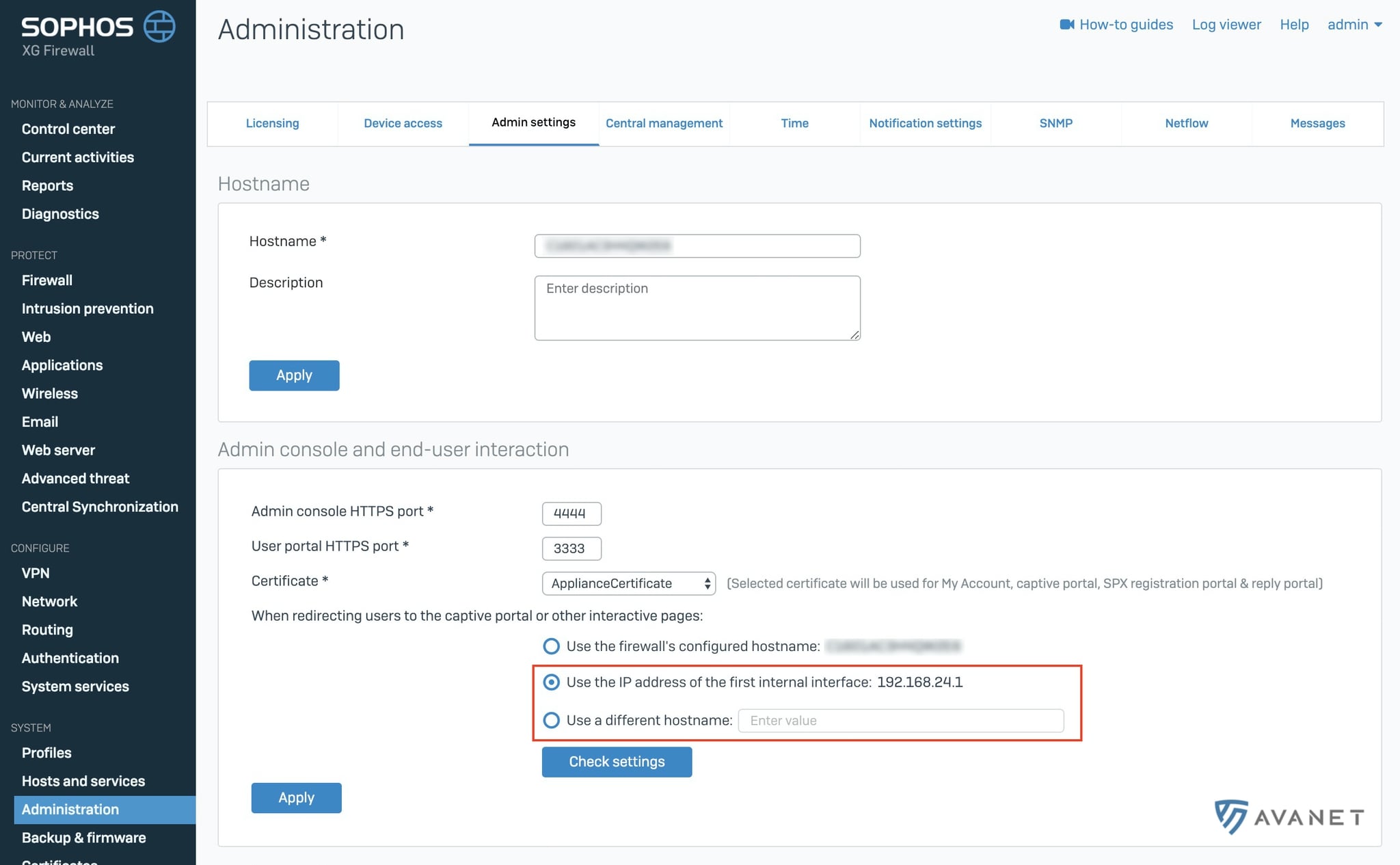
However, switching from an IP address to a web URL only works for the web part. If your XG Firewall is also scanning email, it is common for users to receive a quarantine report from the firewall. This report shows which emails the Sophos firewall has blocked. With a click on a link, you can manually release a supposed spam message. But this link is still an IP address, which works technically, but results in a certificate warning for the user.
The switch from an IP address to a web URL has not yet been implemented for the email part. Sophos has told me that this may be delivered with MR1 or MR2 and that the developers are working on it. I would personally bet on MR2, which means we can probably expect it around January or February.
Synchronized User ID
One of the most common tasks a firewall has to perform is to transport traffic from A to B, provided a firewall rule exists for it. The traffic always originates from and goes to an IP address. As administrators, we like to know which devices are generating the traffic – or even better, which user. This helps us create user-based firewall rules, provide network transparency, and produce more meaningful reports.
On SFOS, there are a few options for identifying the user. In the past, we usually used a connection to an Active Directory server, which forwarded the user information to the XG Firewall via an installed agent. In some environments, however, this agent was not an option.
With SFOS v17.5, endpoints in an Active Directory domain can now share the user identity with the firewall via Security Heartbeat. This makes user identification seamless and easy without having to deploy an agent on the domain controllers. This function can be very helpful in many situations.
Terminal servers or Linux hosts are not covered by this solution. For the former, STAS is still the best option. But the exceptions are significant. Mac clients do not work with Active Directory, and VPN users also do not log on to it.
You can only benefit from this feature if one of the following products is installed on the clients:
In my opinion, it will become really interesting when clients that are not part of a domain can also share their user data with the XG. As it stands, this function solves only a very small problem.
Sophos Connect IPsec VPN client
Our article SSL VPN Client installieren is one of the most popular posts in our knowledge base. For good reason: for many of our customers, VPN was one of the most frequently mentioned requirements before buying the Sophos firewall.
As described in that guide, we currently use the Sophos SSL VPN client very often. However, it can only be installed on Windows computers. On macOS, you previously had to rely on third-party tools such as “Tunnelblick”.
With Sophos Connect, Sophos is now introducing its own IPsec VPN client, as other vendors do as well. Sophos Connect supports Synchronized Security out of the box. This has also worked with the SSL VPN client up to now, but required additional configuration.
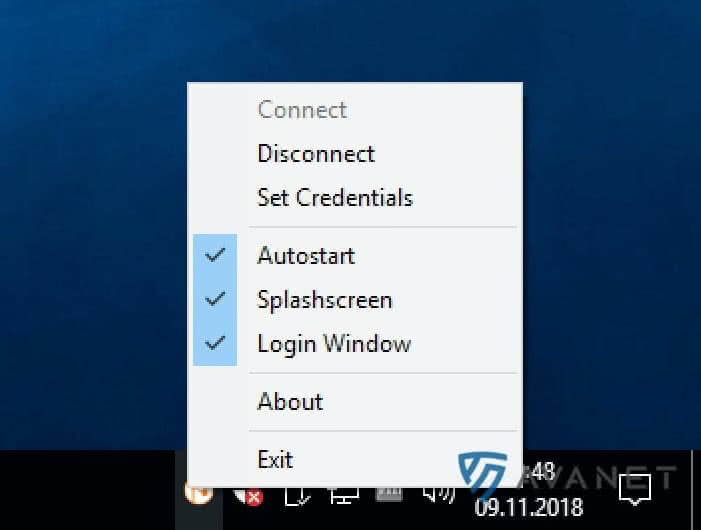
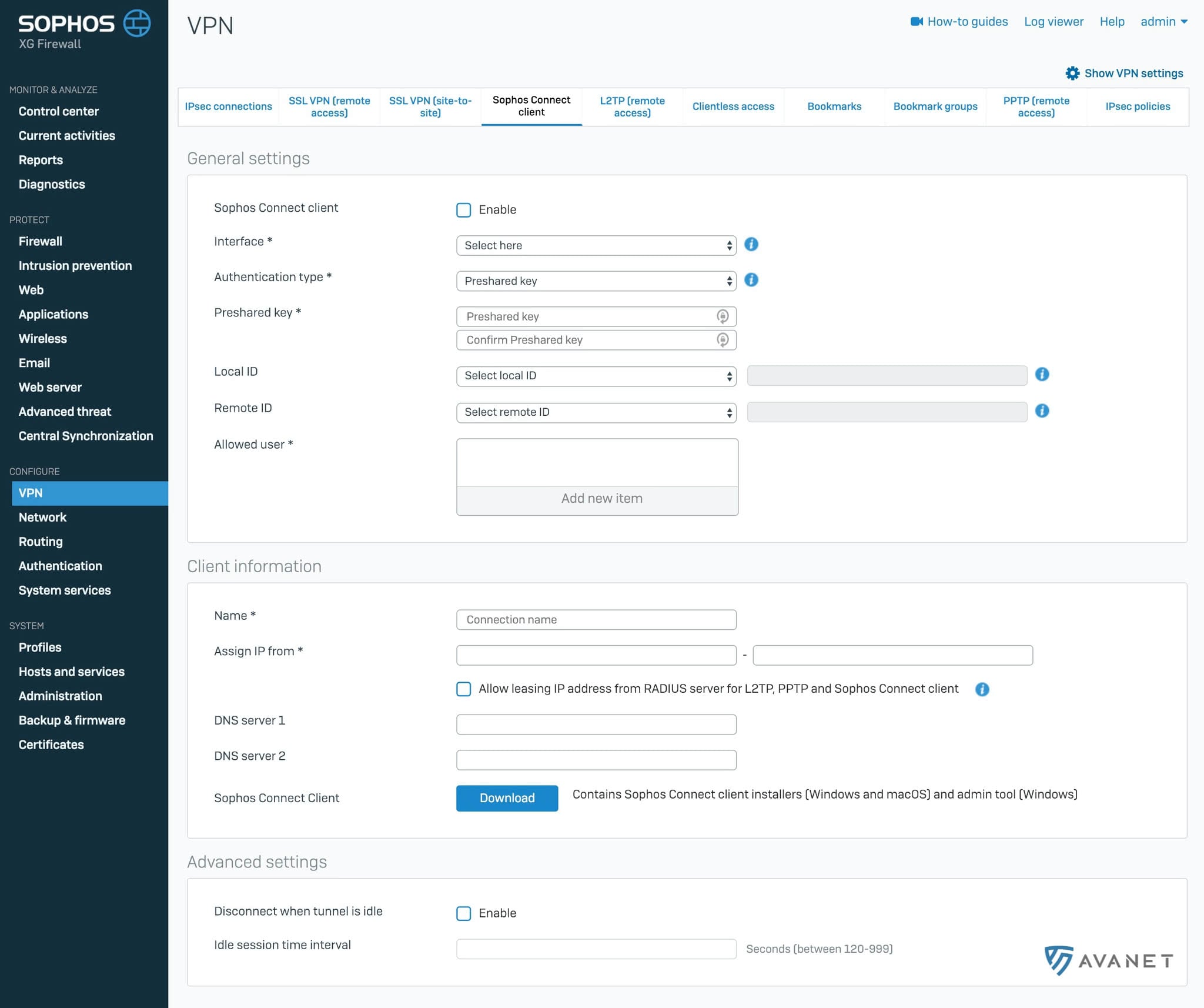
Here is a screenshot showing what the Sophos Connect IPsec VPN client settings look like on the XG Firewall:
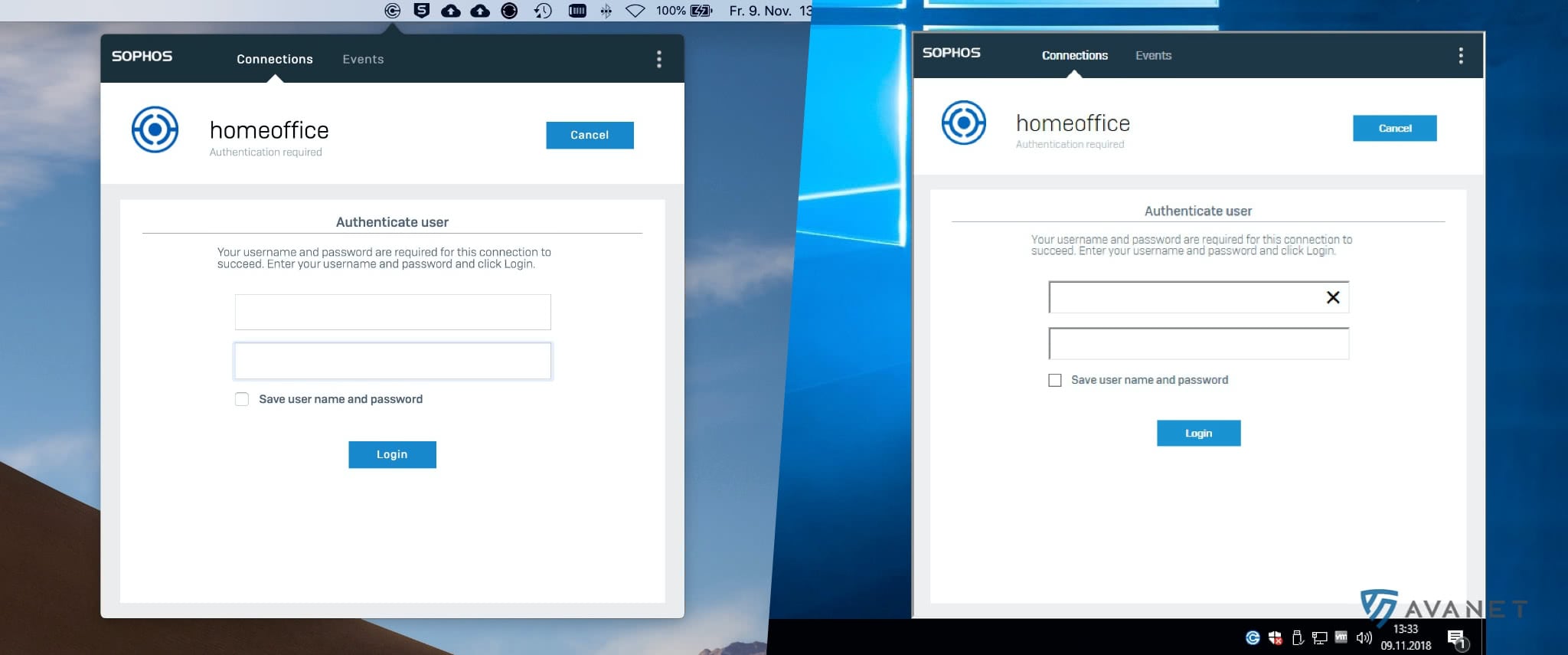
Sophos Connect is currently in beta and the client is available for Windows and macOS. Here is another screenshot of the Mac and Windows clients:
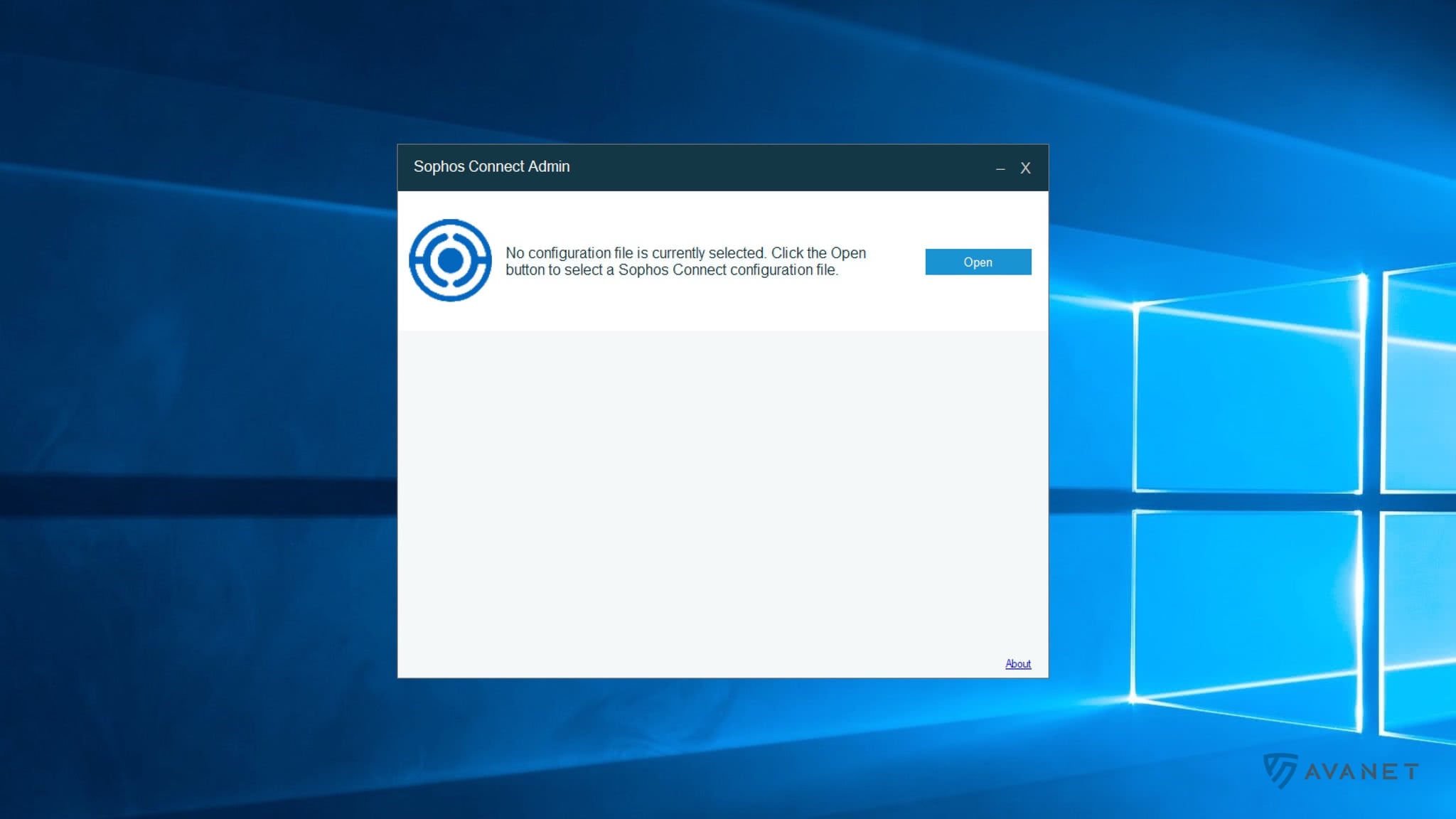
In addition to the new IPsec VPN client from Sophos, there is also “Sophos Connect Admin” as another tool. With it, you can edit a config file afterward, for example, to adjust the hostname or enable 2FA.
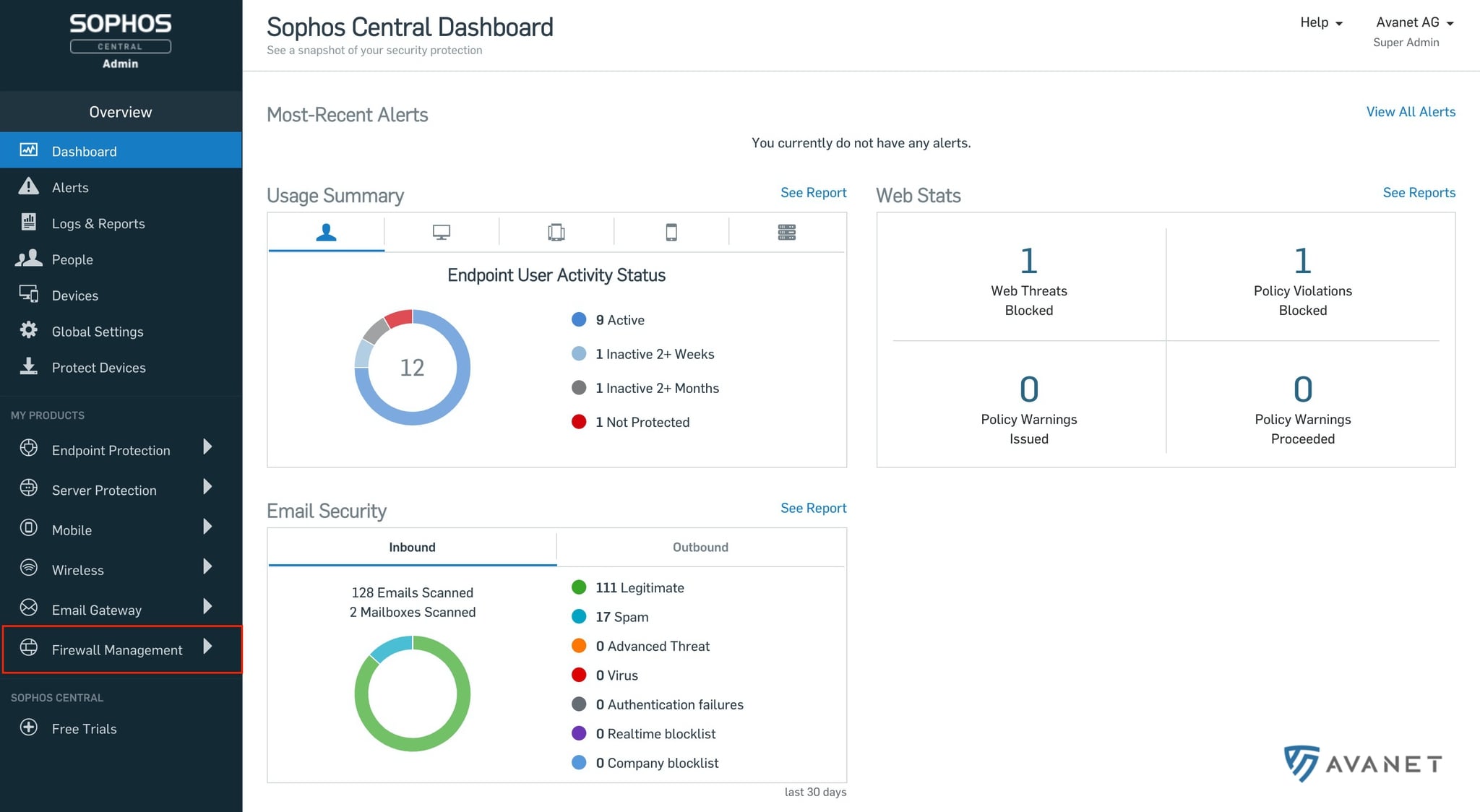
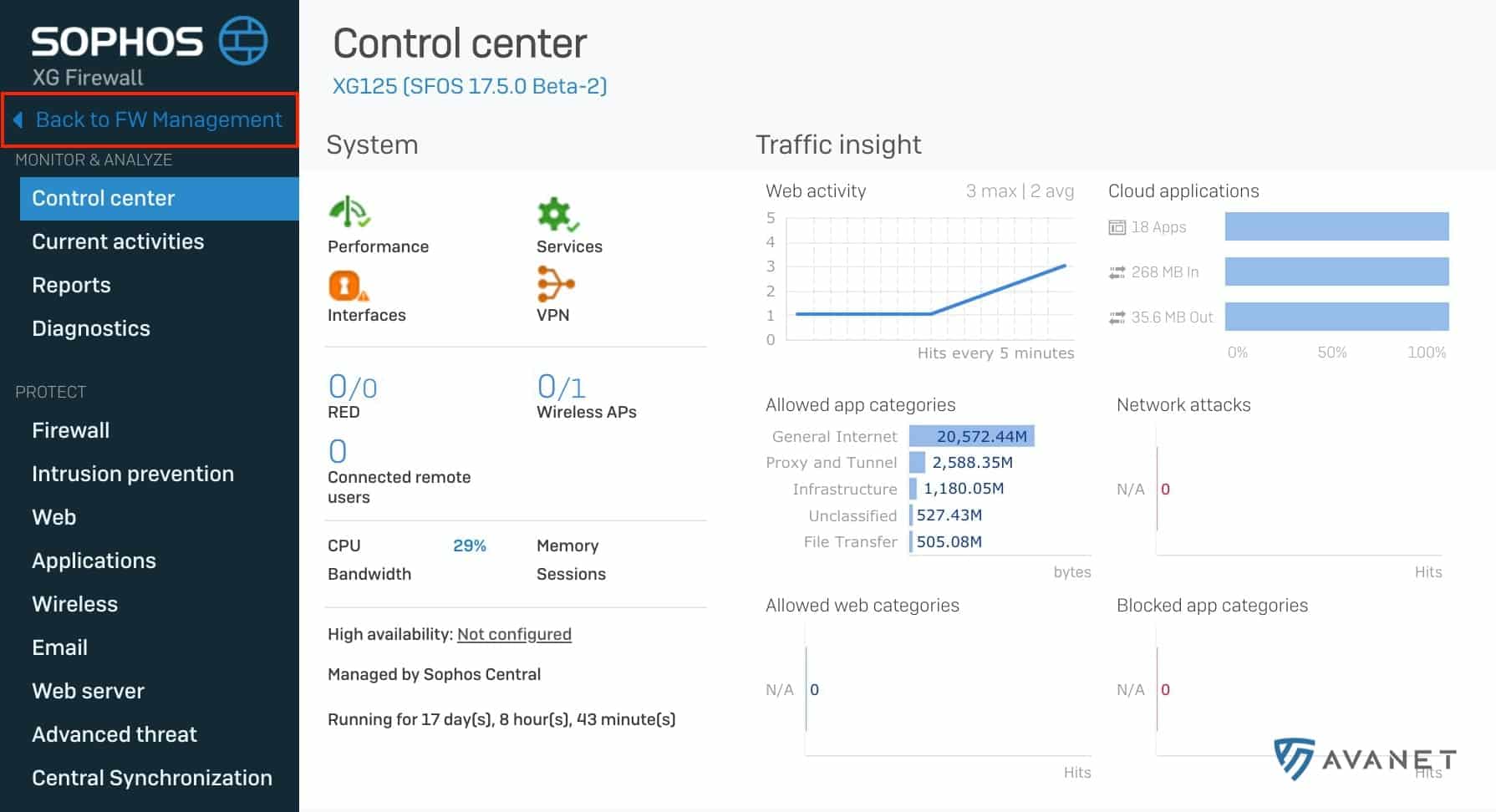
Sophos Central Management
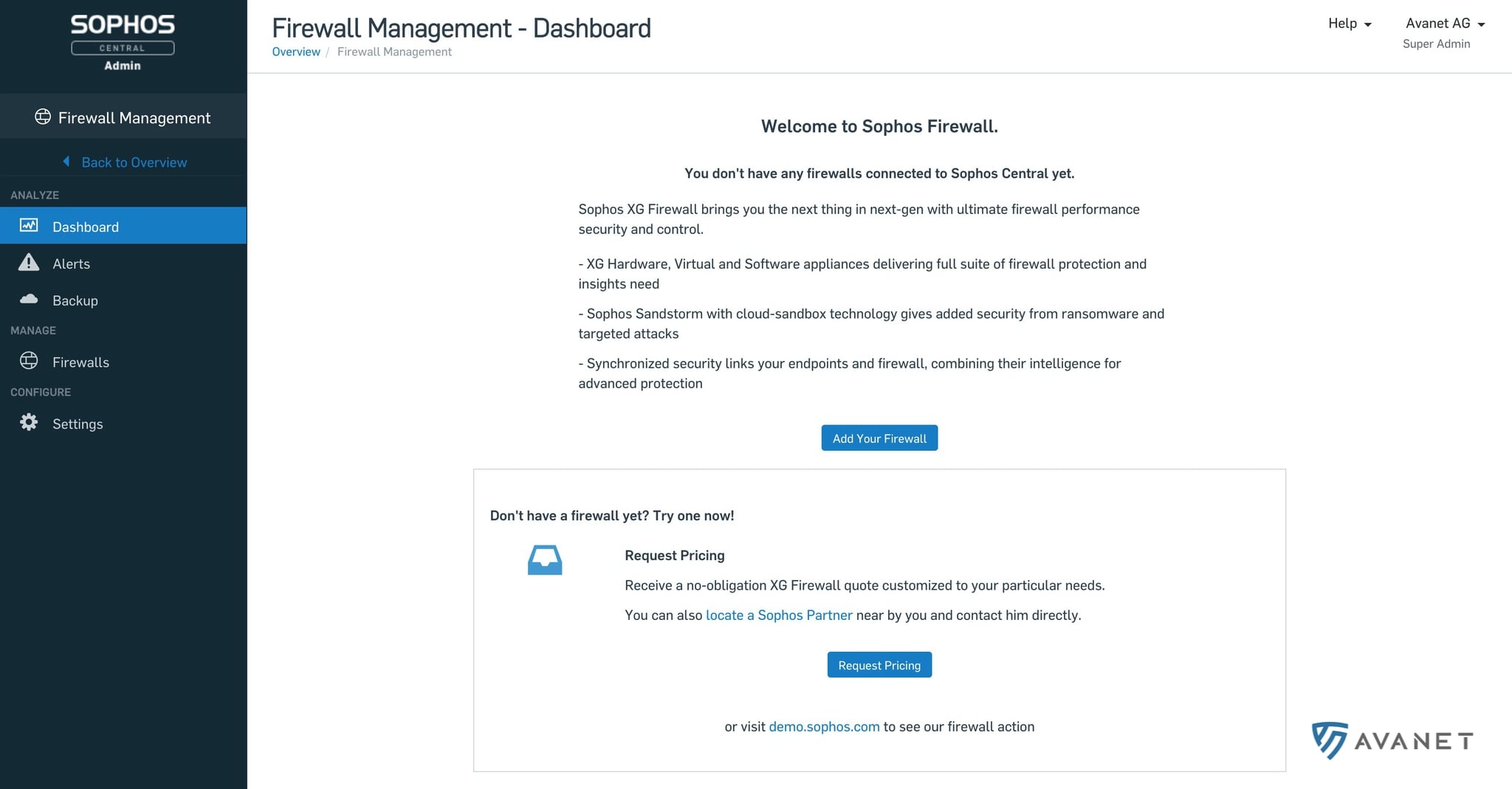
With the new SFOS 17.5 firmware, a long-standing promise is finally being fulfilled. Via the Sophos Central platform, you can now also manage the XG Firewall. Certainly the right step, but in this first version, the functionality is still quite limited.
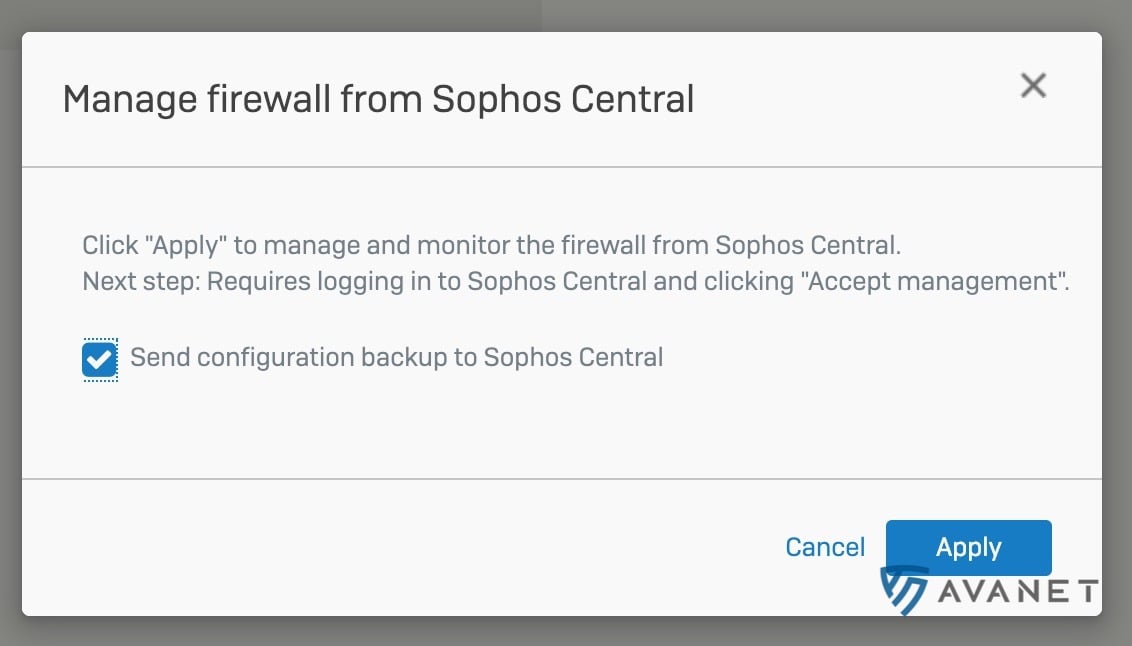
To connect your Central account to the firewall, you first need to enable Central Management on the XG Firewall.
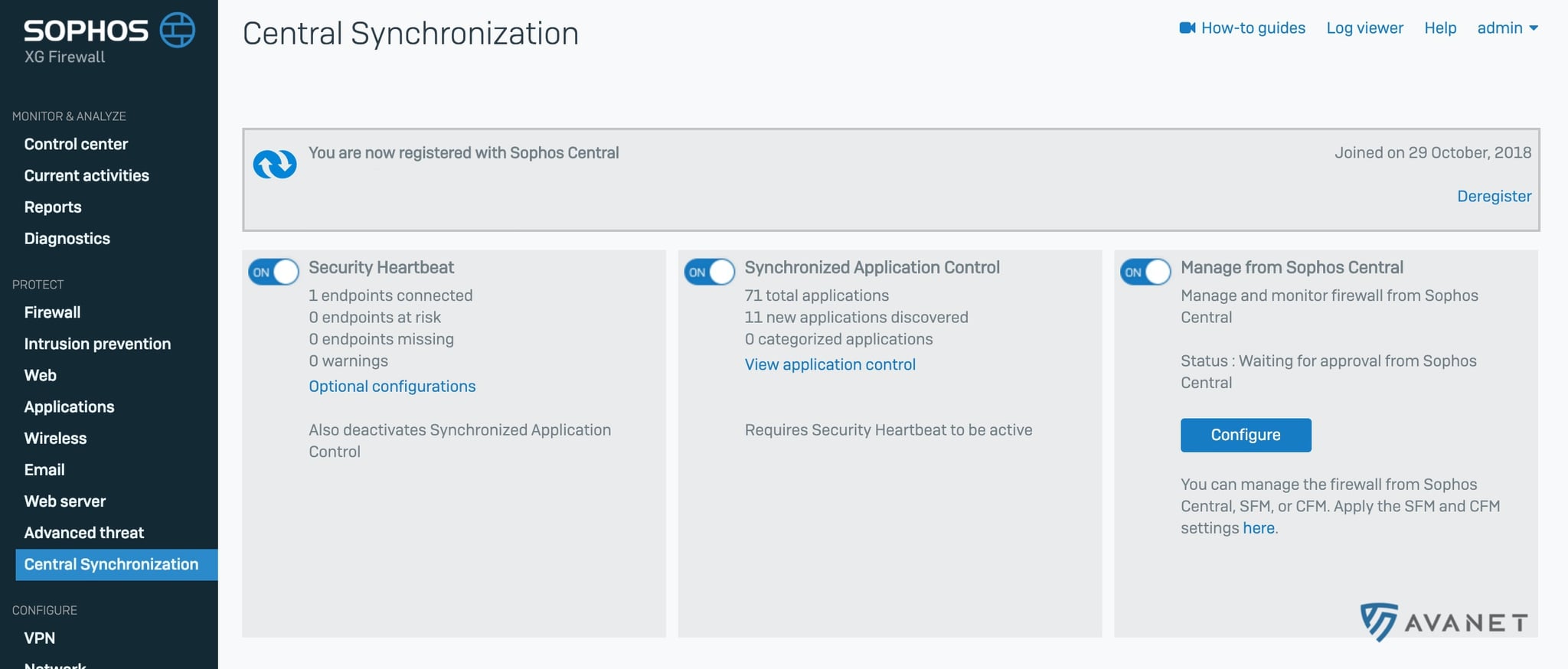
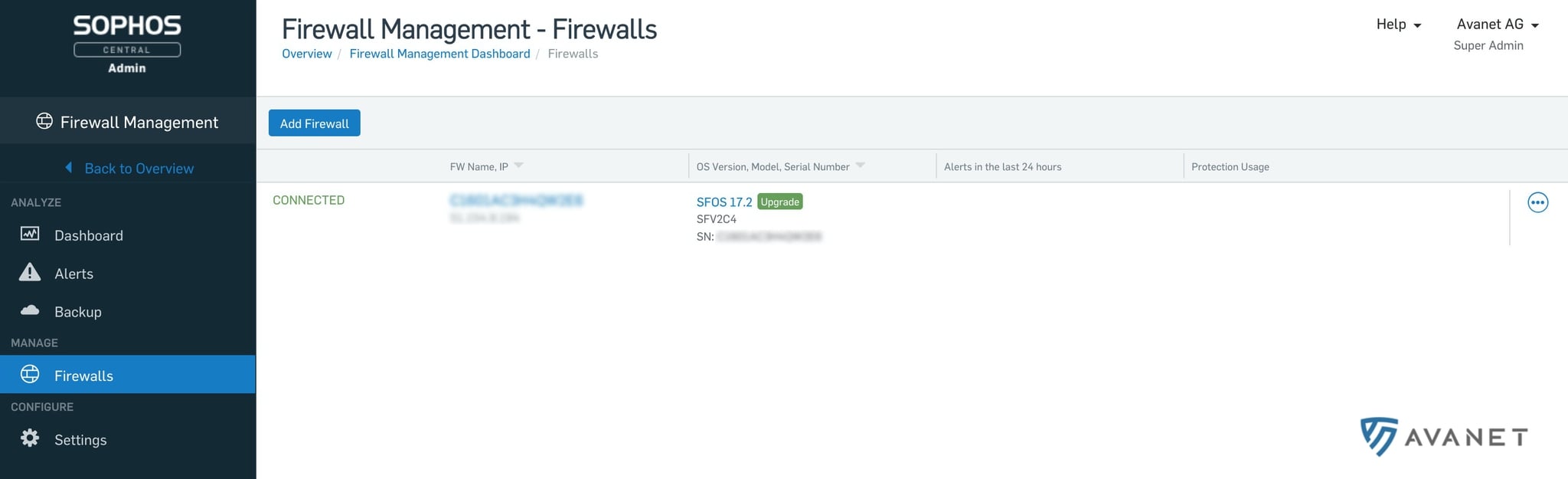
Update 20.11.2018 In the meantime Sophos Central has received an update that now exposes the “Firewall Management” menu item. By enabling the “Central Management” function on our XG Firewall we were able to successfully register the device in our Sophos Central account.
When you connect to the firewall through Sophos Central, you are logged on to the firewall as “admin”. The unfortunate part is that, in theory, other users who have access to Sophos Central Admin can also access the firewalls. It is enough for these users to have read-only permission. We hope that in the future, there will be more fine-grained control over who is allowed to log in to firewalls via Central.
Firewall management via SSO
If you have enabled “Central Management” on your firewall, you can log in to the Sophos XG Firewall directly from the Central interface without an additional login.
Central backups
When Central Management is enabled, backups of your firewall are also stored in Central by default. If you don’t want this, you can simply disable this function on your XG Firewall.
“Light-touch deployment” is a really cool feature. In the future, it will be possible to configure a new XG Firewall directly via Central. You first click your way through a small wizard that outputs an XG config file at the end. You can then download this configuration and copy it to a USB stick. Afterward, you start the new firewall with this stick, and the configuration is applied. If everything has been done correctly, you can reach the firewall via Sophos Central and complete the remaining configuration.
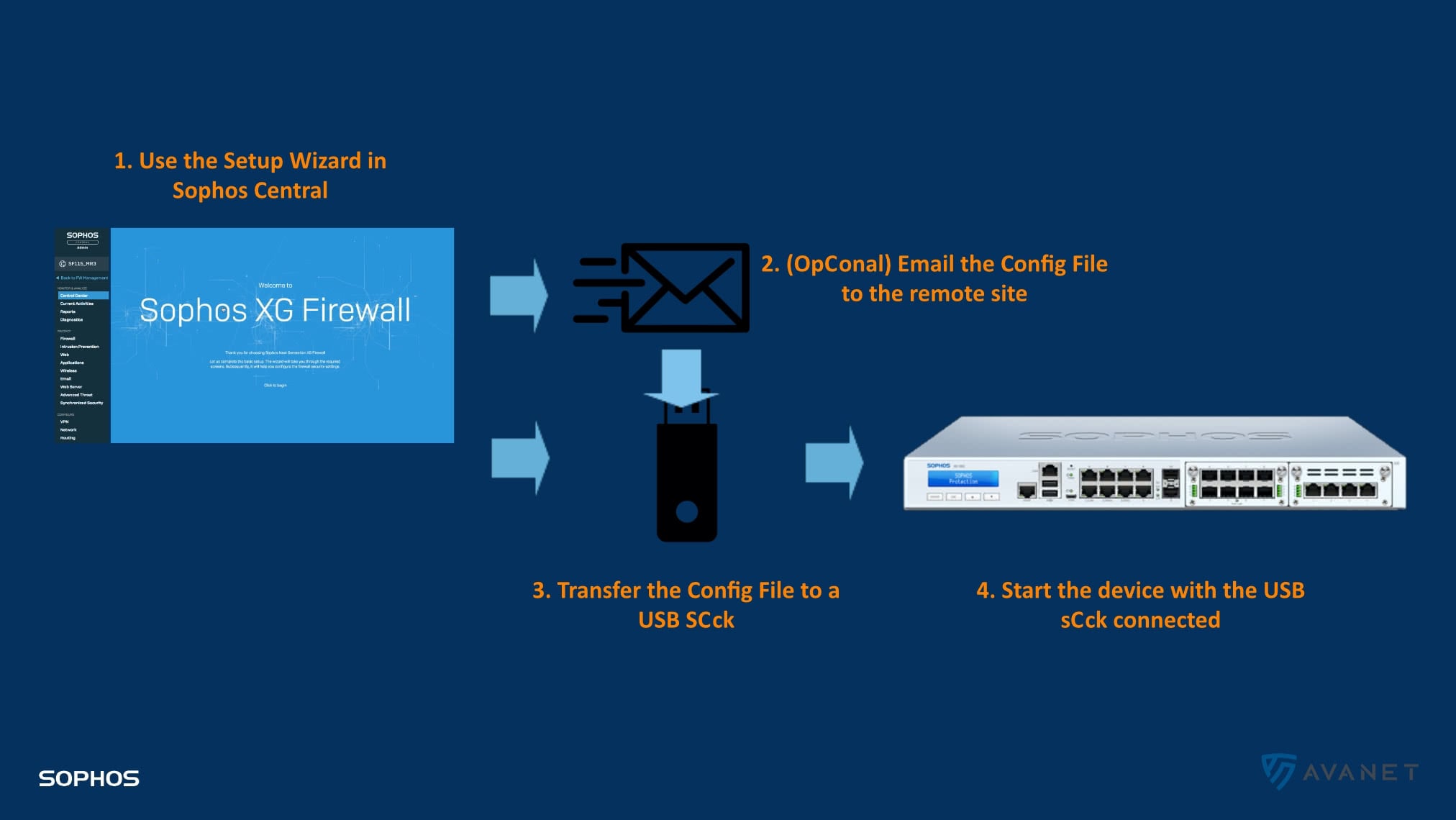
Light-touch deployment will make it much easier for us to set up XG Firewalls for our customers in the future. For our setup and configuration service, we currently have the firewalls sent to our office and create the base configuration directly on the devices. We then send them on to the customer, who only has to connect the firewall to the network. With light-touch deployment, we can save ourselves the shipping of the hardware to us and are at least a day faster. 😎
Because this workflow requires a Central account, we will probably not be able to use this approach for every new customer.
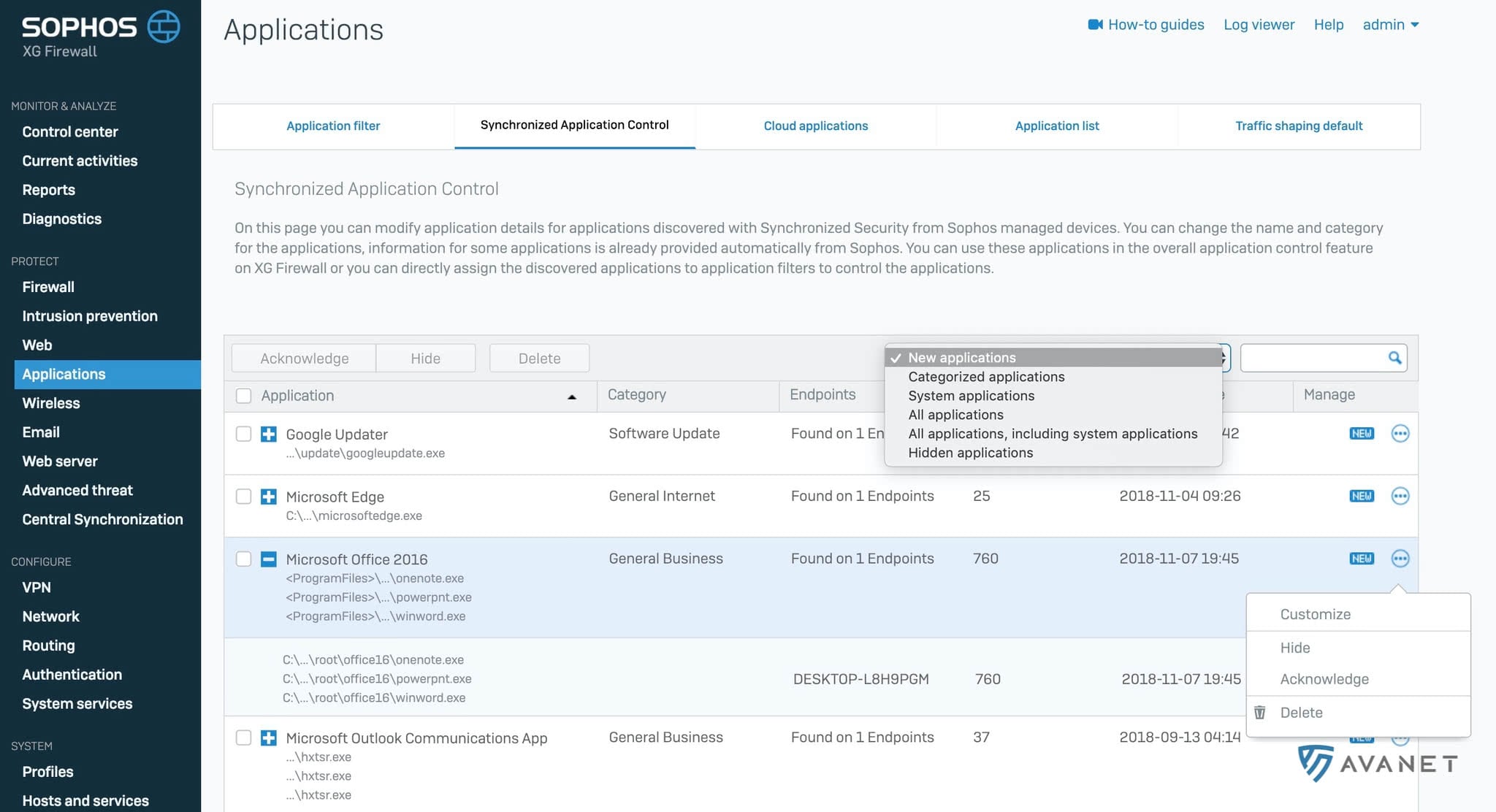
Synchronized Security – Synchronized Application Control improvements
Synchronized Application Control was introduced in version 17.0 and further improved in version 17.1. With this feature, Sophos wanted to address the fundamental problem that a large part of network traffic is still difficult to control and can pass through the firewall relatively unnoticed, even with HTTP/HTTPS scanning. With Synchronized Application Control, the endpoint tells the firewall which software is actually generating the traffic, which allows network traffic to be classified much more accurately.
The following improvements have been implemented in v17.5:
- View Windows and Mac system applications in a separate list.
- Hide applications and then use a new filter option to display hidden applications and to show or hide applications.
- A new option to tag applications so that they are removed from the “new” list.
- Improved display of path names.
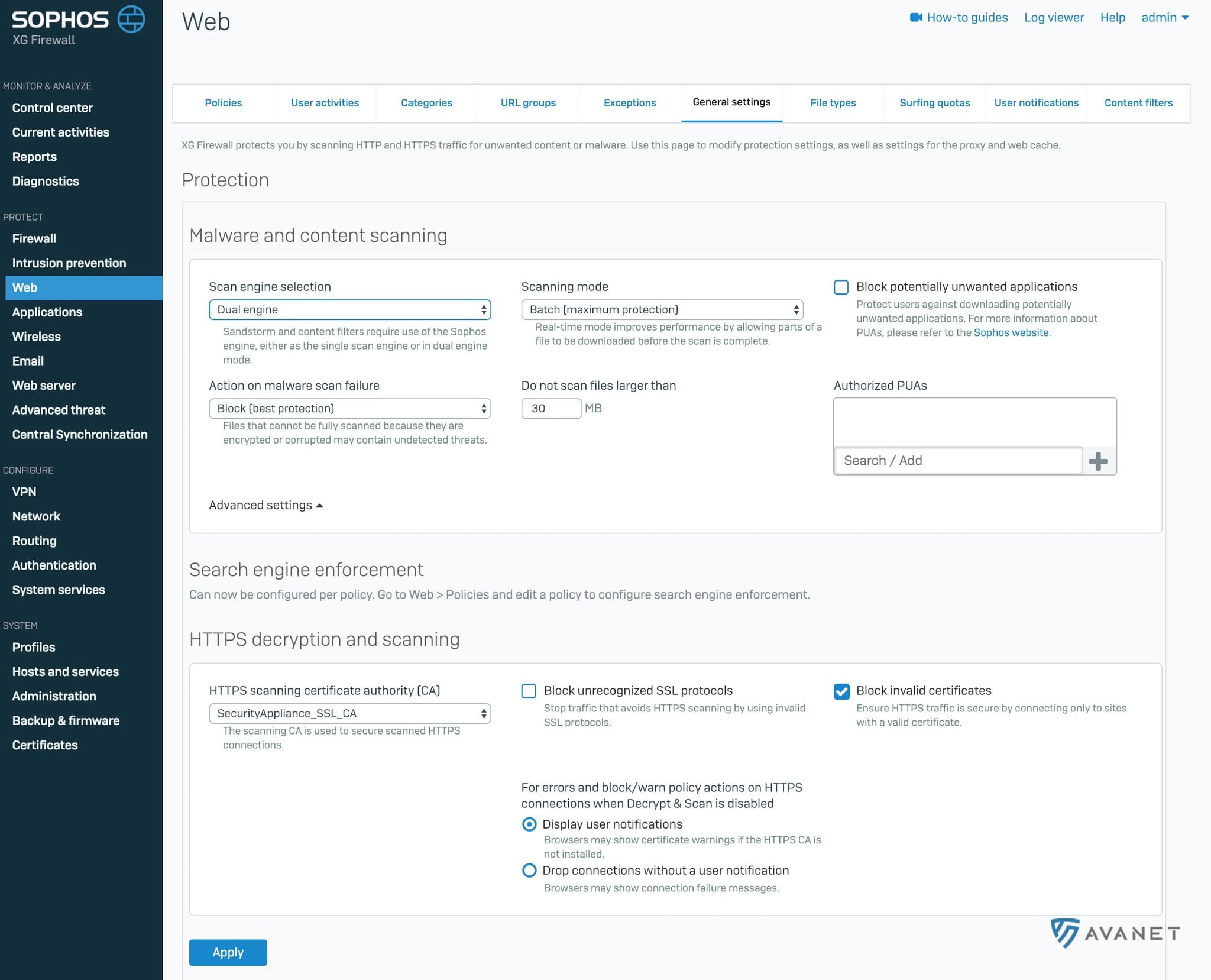
Web policy improvements
Imagine a teacher working with their class on the computer and a required website is blocked. In such a situation the admin has always had to be called in to unblock the site. In SFOS version 17.5 there is now a function in the web policies that allows you to let authorised users access blocked websites anyway. For example, you could give this teacher the ability to unblock this website, domain or category themselves via the User Portal.
Each rule receives a code that the teacher can then share with the class. On the blocked page the students can enter this code and will temporarily be allowed to access the otherwise blocked website.
As administrators we can then see in a list which codes have been generated and can also delete them again. The admin can also define locations or categories that teachers are not allowed to override.
Here are a few more small new features that will be available to you in SFOS version 17.5 in the web policies:
- Setting a default search engine
- SafeSearch and YouTube restrictions
- Limiting file size when downloading
- Google App domain restrictions configured per policy
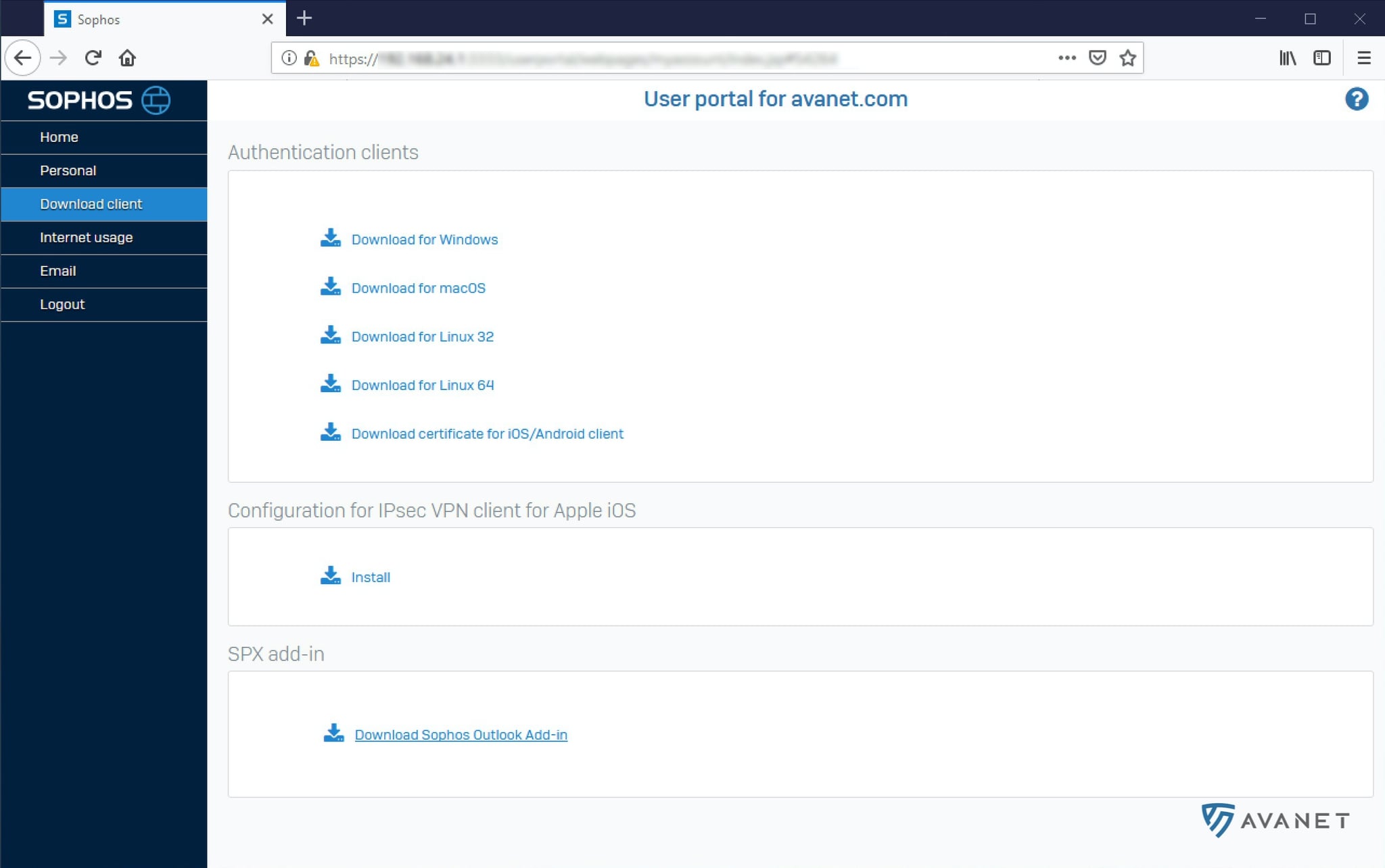
Client Authentication Agent
The XG Firewall Client Authentication Agent provides a way to tell the XG Firewall which user is currently logged in on a computer without Active Directory. For this, you simply run the Client Authentication Agent on the device.
The client is available for Windows, macOS, Linux 32/64 bit, iOS, and Android. You can find the download in the User Portal.
Management improvements
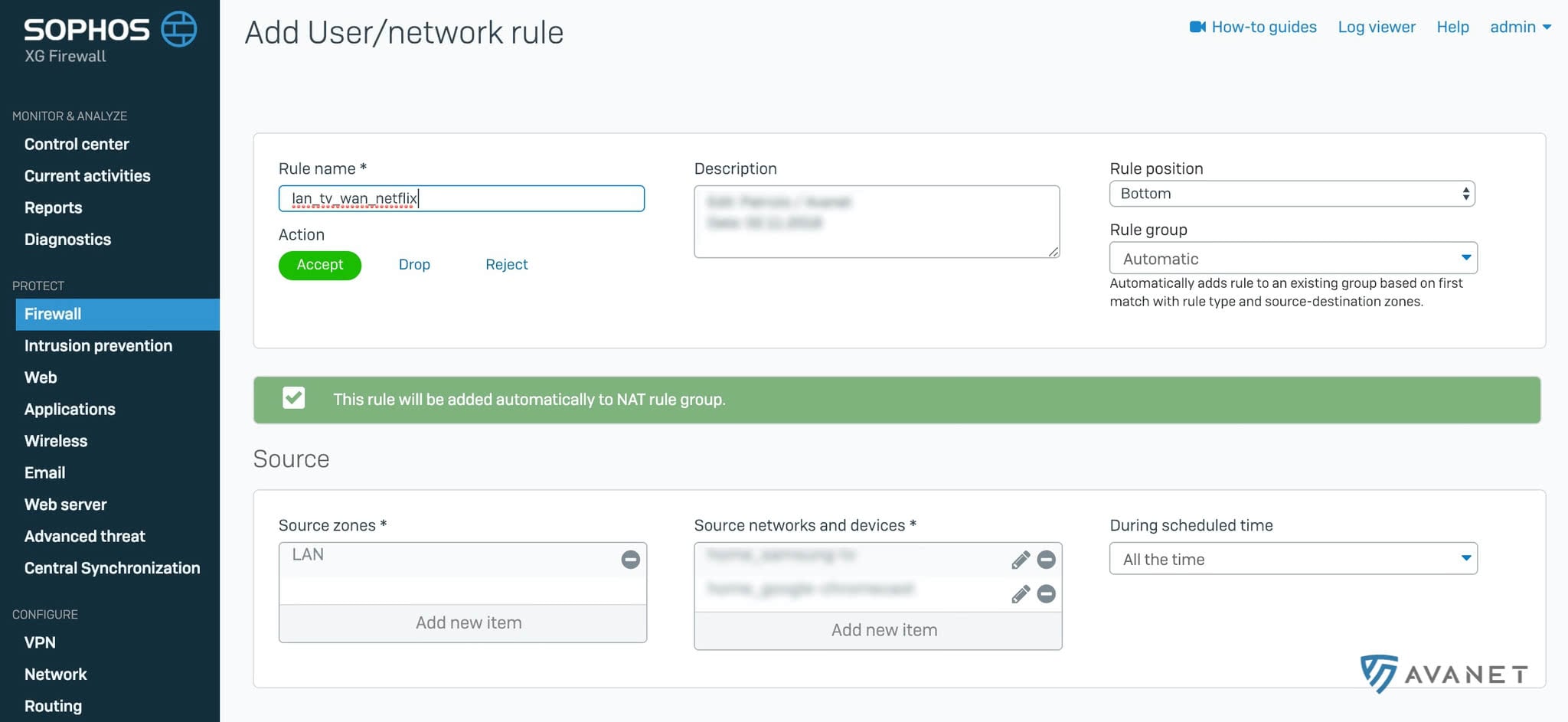
When you create a new firewall rule, you can now assign it to a group right away. There is also a new automatic group assignment, although this did not work particularly well for me. In my tests, the firewall wanted to assign my rule automatically to a group I did not want it to be in.
IPS Protection
- More categories to fine-tune the rules even better, providing improved performance and more protection.
Wireless
- Support for RADIUS server failover with multiple servers.
IPsec
- SD-WAN failover and failback
- IPsec failover – redundant groups for IPsec connections so that in the event of a failover, the connection can switch to another WAN link. As soon as the primary connection is available again, it can switch back.
What’s coming in the next versions?
In the coming weeks and months, maintenance releases will appear as usual that will deliver a number of additional features.
Sophos Wireless APX access point support
The new APX access points from Sophos could previously only be used with Sophos Central. Support for the XG Firewall is expected in MR1, which should appear around two to four weeks after the 17.5 release. The APX 120, which is supposed to be available for under 200 CHF, will not arrive until January 2019.
Airgap support
There are XG Firewalls that are not connected to the internet. Until now, it has not been possible to activate a license on these devices. Now there is an option to load the license and updates onto the firewall via a USB stick.